CRS317-1G-16S+ RouterOS 7.22.1
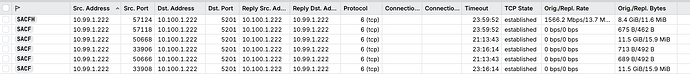
Goal: Firewall traffic from vlan99 to only allow specific host/port access to stuff in vlan100 and offload allowed traffic to get close to line speed.
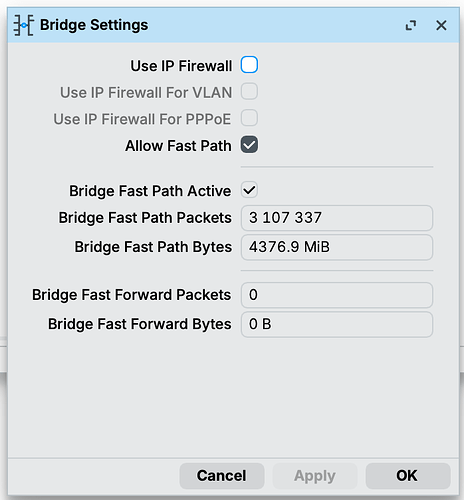
So I’ve had this in my rack for a while working without issue, but recently I’ve tried to use some of the L3 features to do inter-vlan routing for interfaces on the same bridge. More specifically even with the in/out on the same interfaces. From everything I’ve read this should work but I just can’t seem to get any connections to be fast tracked. With firewall rules in place all processing is done on the cpu and with iperf between vlans I’m only getting ~500mbps. With rules removed and switch ports set with l3-hw-offloading=yesI can get the full line rate at ~9.6gbps.
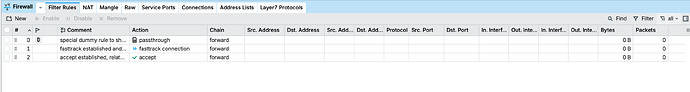
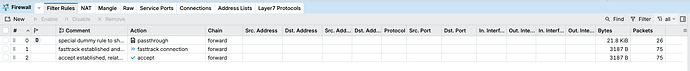
The counters for the dummy fast track firewall rule have always been empty indicating none of the traffic is being fast tracked. I’ve also rebooted the switch multiple times. Even resorted to updating to the latest 7.x release with no change.
Config
[admin@mt-rack-switch-10g] > export compact
# 2026-04-03 09:10:42 by RouterOS 7.22.1
# software id = NFFW-76TF
#
# model = CRS317-1G-16S+
# serial number = D7EC0EFC3BA5
/interface bridge
add admin-mac=2C:C8:1B:FD:9D:88 auto-mac=no comment=defconf ingress-filtering=no name=bridge port-cost-mode=short vlan-filtering=yes
/interface ethernet
set [ find default-name=sfp-sfpplus1 ] comment=pve1
set [ find default-name=sfp-sfpplus2 ] comment=pve2
set [ find default-name=sfp-sfpplus3 ] comment=pve3
set [ find default-name=sfp-sfpplus13 ] comment=storage
set [ find default-name=sfp-sfpplus15 ] comment="bonding1 rack-switch"
set [ find default-name=sfp-sfpplus16 ] comment="bonding1 rack-switch"
/interface vlan
add interface=bridge name=vlan10 vlan-id=10
add interface=bridge name=vlan99 vlan-id=99
add interface=bridge name=vlan100 vlan-id=100
add interface=bridge name=vlan101 vlan-id=101
add interface=bridge name=vlan102 vlan-id=102
add interface=bridge name=vlan200 vlan-id=200
/interface bonding
add comment=rack-switch mode=802.3ad name=bonding1 slaves=sfp-sfpplus15,sfp-sfpplus16
/interface ethernet switch port
set 0 l3-hw-offloading=no
set 1 l3-hw-offloading=no
set 2 l3-hw-offloading=no
set 3 l3-hw-offloading=no
set 4 l3-hw-offloading=no
set 5 l3-hw-offloading=no
set 6 l3-hw-offloading=no
set 7 l3-hw-offloading=no
set 8 l3-hw-offloading=no
set 9 l3-hw-offloading=no
set 10 l3-hw-offloading=no
set 11 l3-hw-offloading=no
set 12 l3-hw-offloading=no
set 13 l3-hw-offloading=no
set 14 l3-hw-offloading=no
set 15 l3-hw-offloading=no
set 16 l3-hw-offloading=no
/interface list
add name=VLAN99_IN
/interface lte apn
set [ find default=yes ] ip-type=ipv4 use-network-apn=no
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/system logging action
add name=syslog remote=10.100.1.13 remote-log-format=syslog syslog-facility=local0 target=remote
/interface bridge port
add bridge=bridge ingress-filtering=no interface=ether1 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus1 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus2 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus3 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus4 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus5 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus6 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus7 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus8 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus9 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus10 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus11 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus12 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus13 internal-path-cost=10 path-cost=10
add bridge=bridge interface=sfp-sfpplus14 internal-path-cost=10 path-cost=10
add bridge=bridge interface=bonding1 internal-path-cost=10 path-cost=10
/interface ethernet switch l3hw-settings
set autorestart=yes
/ip firewall connection tracking
set udp-timeout=10s
/ip settings
set max-neighbor-entries=8192
/ipv6 settings
set disable-ipv6=yes max-neighbor-entries=8192 soft-max-neighbor-entries=8191
/interface bridge vlan
add bridge=bridge tagged=bridge,ether1,bonding1,sfp-sfpplus1,sfp-sfpplus2,sfp-sfpplus3,sfp-sfpplus13 vlan-ids=100
add bridge=bridge tagged=bridge,ether1,bonding1,sfp-sfpplus1,sfp-sfpplus2,sfp-sfpplus3 vlan-ids=101
add bridge=bridge tagged=bridge,ether1,bonding1 vlan-ids=102
add bridge=bridge tagged=bridge,ether1,bonding1,sfp-sfpplus1,sfp-sfpplus2,sfp-sfpplus3,sfp-sfpplus13 vlan-ids=10
add bridge=bridge tagged=bridge,bonding1,sfp-sfpplus1,sfp-sfpplus2,sfp-sfpplus3 vlan-ids=200
add bridge=bridge tagged=bridge,bonding1,sfp-sfpplus1,sfp-sfpplus2,sfp-sfpplus3,sfp-sfpplus13 vlan-ids=99
/interface ethernet switch
set 0 l3-hw-offloading=yes
/interface list member
add interface=vlan99 list=VLAN99_IN
/ip address
add address=10.100.1.21/24 interface=vlan100 network=10.100.1.0
add address=10.99.1.2/24 interface=vlan99 network=10.99.1.0
/ip dns
set servers=10.100.1.2,10.100.1.3,10.100.1.1
/ip firewall filter
add action=fasttrack-connection chain=forward comment="fasttrack established and related connection states" connection-state=established,related
add action=accept chain=forward comment="accept established, related and untracked connection states" connection-state=\
established,related,untracked
/ip hotspot profile
set [ find default=yes ] html-directory=hotspot
/ip ipsec profile
set [ find default=yes ] dpd-interval=2m dpd-maximum-failures=5
/ip route
add disabled=no dst-address=0.0.0.0/0 gateway=10.100.1.1
/ip ssh
set password-authentication=yes
/ipv6 nd
set [ find default=yes ] advertise-dns=yes
/routing bfd configuration
add disabled=no
/system clock
set time-zone-name=America/New_York
/system identity
set name=mt-rack-switch-10g
/system logging
add action=syslog topics=critical
add action=syslog topics=error
add action=syslog topics=warning
/system ntp client
set enabled=yes
/system ntp client servers
add address=10.100.1.2
add address=10.100.1.3