The blog and configurations are available here:
https://stubarea51.net/2020/02/15/mikro ... ook-vxlan/


#***VTEP-01***
# apr/05/2020 13:18:18 by RouterOS 7.0beta5
# software id =
#
/interface bridge
add mtu=9000 name=BRIDGE-VXLAN
/interface ethernet
set [ find default-name=ether1 ] mtu=9000
set [ find default-name=ether2 ] mtu=9000
set [ find default-name=ether3 ] mtu=9000
/interface vxlan
add group=239.0.0.1 interface=ether2 name=vxlan-vni-100 port=8472 vni=100
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/interface bridge port
add bridge=BRIDGE-VXLAN interface=vxlan-vni-100
add bridge=BRIDGE-VXLAN interface=ether3
/interface vxlan vteps
add interface=vxlan-vni-100 remote-ip=10.10.10.2
/ip address
add address=10.10.10.1/30 interface=ether2 network=10.10.10.0
add address=10.100.100.100/24 interface=BRIDGE-VXLAN network=10.100.100.0
/ip dhcp-client
add add-default-route=no disabled=no interface=ether1
#error exporting /ipv6/route/rule
#error exporting /routing/policy/selection
/system identity
set name=VTEP-01
/tool sniffer
set filter-interface=ether3
#
#
#***VTEP-02***
# apr/05/2020 13:20:48 by RouterOS 7.0beta5
# software id =
#
/interface bridge
add mtu=9000 name=BRIDGE-VXLAN
/interface ethernet
set [ find default-name=ether2 ] mtu=9000
set [ find default-name=ether3 ] mtu=9000
/interface vxlan
add group=239.0.0.1 interface=ether2 name=vxlan-vni-100 port=8472 vni=100
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/interface bridge port
add bridge=BRIDGE-VXLAN interface=ether3
add bridge=BRIDGE-VXLAN interface=vxlan-vni-100
/interface vxlan vteps
add interface=vxlan-vni-100 remote-ip=10.10.10.1
/ip address
add address=10.10.10.2/30 interface=ether2 network=10.10.10.0
add address=10.100.100.200/24 interface=BRIDGE-VXLAN network=10.100.100.0
/ip dhcp-client
add add-default-route=no disabled=no interface=ether1
#error exporting /ipv6/route/rule
#error exporting /routing/policy/selection
/system identity
set name=VTEP-02
/tool sniffer
set filter-interface=ether3
Yes you can. VXLAN-Interface forms a transparent L2 tunnel, so you can use IPv6 inside it.can I use ipv6 over ipv4? that is vtep will be ipv4 but servers will communicate on ipv6.
i was wondering about that too. or via wireguard maybeWhat about VxLAN over IPsec?
vxlan via L2tp+ipseci was wondering about that too. or via wireguard maybeWhat about VxLAN over IPsec?
vxlan via L2tp+ipsec
i was wondering about that too. or via wireguard maybe
what is the point doing that?
a encrypted layer2 (as overlay of a layer3 net) link obviously
vxlan via L2tp+ipsec
what is the point doing that?
got it working last month with wireguard.
on 2 hEX S it pushes around 200mbit both directions (far from wire/line speed as one could see with MACsec but on a 100mbit interconnect it is enough)
you got EVE-NG? i'll export a basic setupDo you have a vxlan over wireguard example.
Im confused as to the local address I assumed these would be addresses anchored to a local wireguard address at each end
just not sure if the VTEP setting applies only to an external vxlan aware device and not used when the MT is the VXlan smart device?
okayNo need, working on it, almost there.........
viewtopic.php?t=194310#p989515
That was effort #3 ( vxlan over wireguard )
effort #2 is through DHCP options
effort #1 is via WG and EOIP ( not yet done as have to deal with where internet comes from on spanned subnets)
All three were to see how one could connect a unifi controller on one router to two APs at another location. Exercise in possibilities and learning new things.
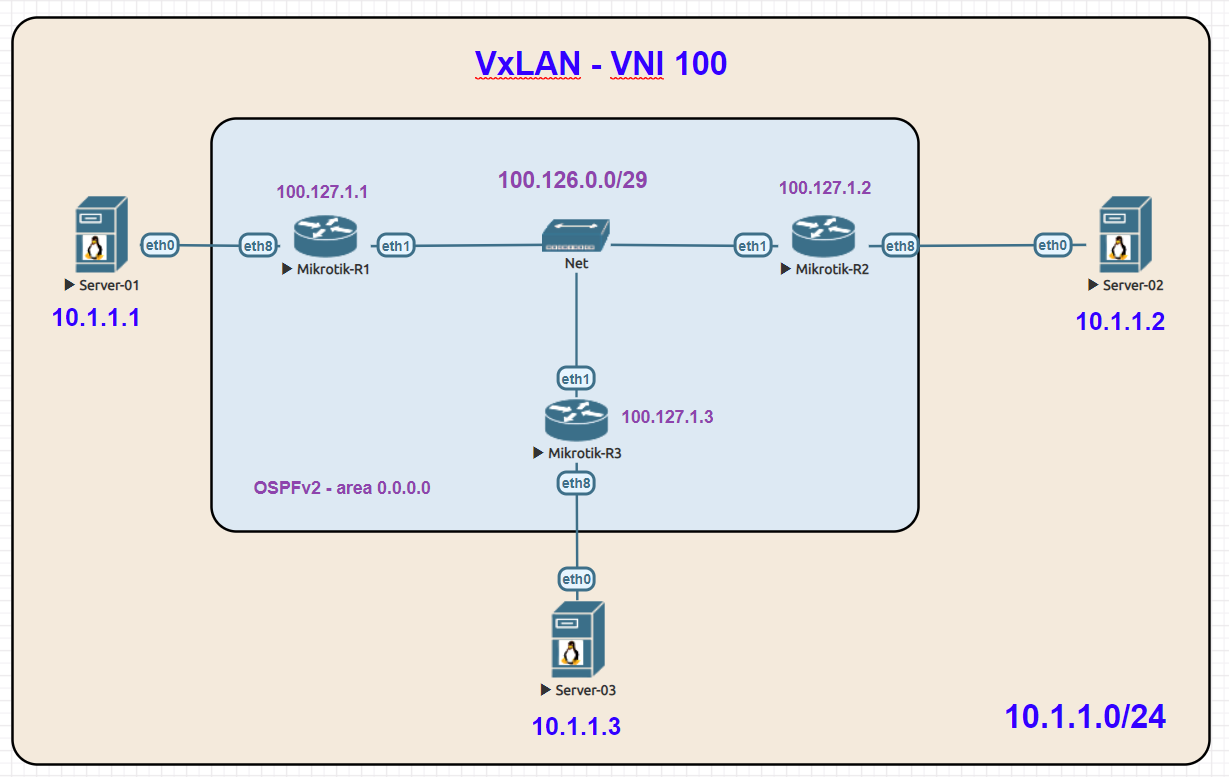
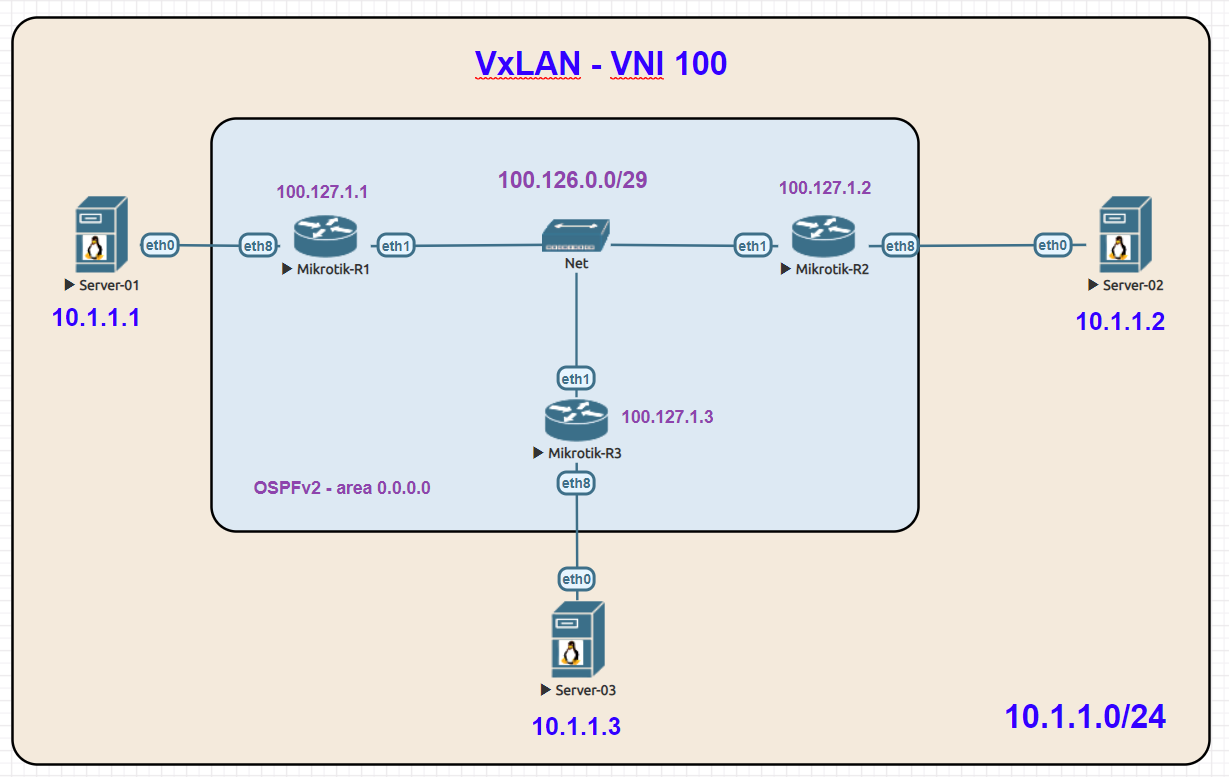
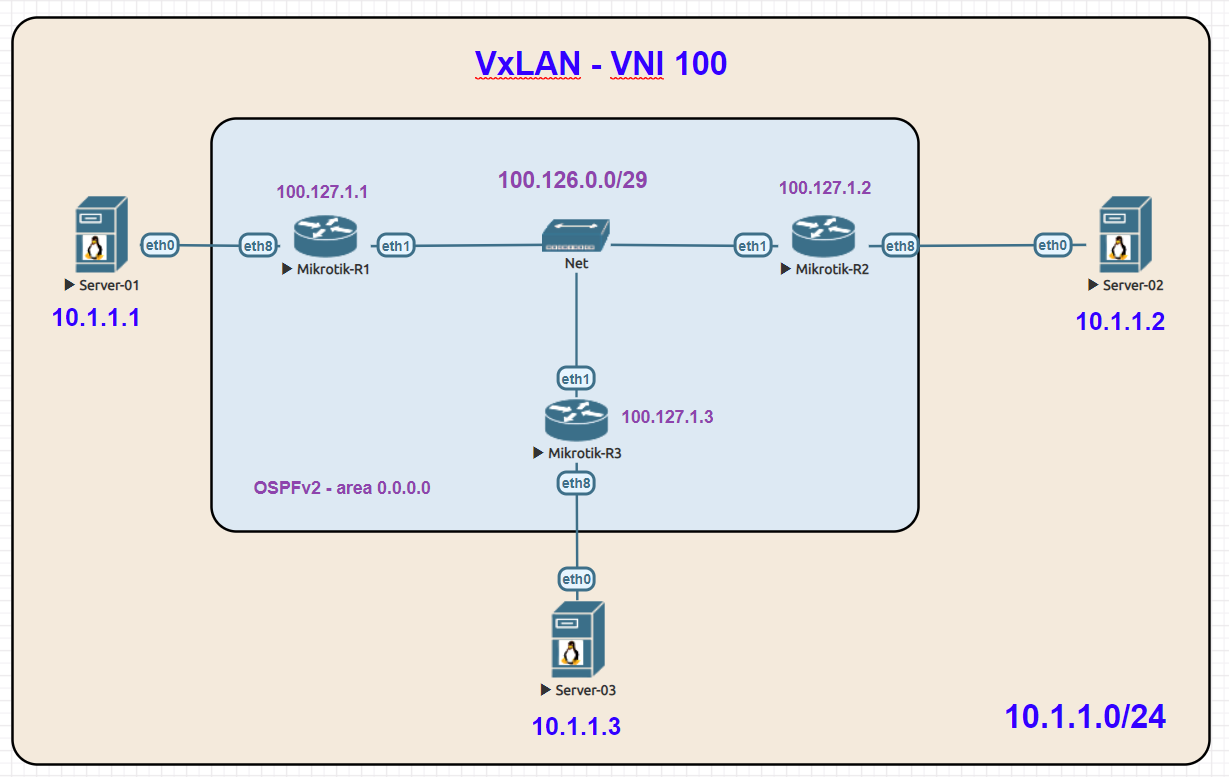
The article forgot to mention some key points ( drawbacks to need to solve )Here is a blog post I did with a VxLAN lab in EVE-NG between 3 routers and 3 linux servers:
The blog and configurations are available here:
https://stubarea51.net/2020/02/15/mikro ... ook-vxlan/