Is it possible to setup an IPSec tunnel to use a specific public address on a WAN interface that consist of a "/29" subnet (i.e any of the 5 public IP addresses) ?
I'm asking since we had some issues with IPsec and the only way to resolve the problem was to pick to the lowest address from the public subnet (Pref. Source according to the routing list). The tunnel is established correctly but cannot pass any packets since the remote peer gets pref-source from the sending side as return address i.e the outbound address = pref-source.
--
Thanks in advance!
Setup IPSec to use specific outbound subnet address on WAN?
Last edited by Larsa on Fri Dec 08, 2017 9:33 am, edited 2 times in total.
-

-
gotsprings
Forum Guru

- Posts: 2121
- Joined:
Re: Setup IPSec to use specific outgoing subnet address on WAN?
I have picked a number off the 5 of a block and it works fine.
Re: Setup IPSec to use specific outgoing subnet address on WAN?
I have picked a number off the 5 of a block and it works fine.
Well, thats what we tried. But the outbound ip address always defaults to Pref Source i.e first usable address in the subnet.
Since you have to use "accept srcnat Src.Addresse Dst.Adresses" as the first entry to bypass any further NAT-traversals, how exactly did you manage to force the outbound ip address to be anything else?
Re: Setup IPSec to use specific outgoing subnet address on WAN?
Any suggestion how this can be solved?
Re: Setup IPSec to use specific outbound subnet address on WAN?
Instead of a direct IPsec tunnel, use GRE over IPsec or L2TP over IPsec to establish a tunnel, and
route your LAN traffic via that tunnel. That will end all your problems with NAT avoidance etc.
route your LAN traffic via that tunnel. That will end all your problems with NAT avoidance etc.
Re: Setup IPSec to use specific outbound subnet address on WAN?
You need to set the "prefered source" on the route - it will set the outbound router ip address.
Re: Setup IPSec to use specific outbound subnet address on WAN?
Dumb questions -just to be sure:
Did you specify that desired address as local-address in the peer definition?
Is that address actually really assigned to the router?
I have a couple of IPsec tunnels running here with multiple WAN addresses and they're running just fine as expected...
-Chris
Did you specify that desired address as local-address in the peer definition?
Is that address actually really assigned to the router?
I have a couple of IPsec tunnels running here with multiple WAN addresses and they're running just fine as expected...
-Chris
Re: Setup IPSec to use specific outbound subnet address on WAN?
Instead of a direct IPsec tunnel, use GRE over IPsec or L2TP over IPsec to establish a tunnel, and
route your LAN traffic via that tunnel. That will end all your problems with NAT avoidance etc.
Hi! Thanks for the suggestion, but In this case it's not the NAT avoidance that is the main issue, but rather the ability to pick an arbitrary outbound ip address in a subnet for a specific tunnel.
Last edited by Larsa on Thu Dec 07, 2017 1:07 pm, edited 1 time in total.
Re: Setup IPSec to use specific outbound subnet address on WAN?
You need to set the "prefered source" on the route - it will set the outbound router ip address.
Ok, so if I understand you correctly pref-source is the only way you can control the outbound address for a IPsec tunnel. So in case you have a "/29" subnet defined for your WAN, then you need to assign pref-source for every indivual address in the subnet that you want to assign as an outbound address for a specific tunnel.
But for a "/29" subnet you only have one pref-source in the routing table, right? How do you solve that, what about using "/32" for each subnet ip or is there any other way? Btw, whould a "/32" subnet on the WAN create any side effects or other impacts you shoud be aware of?
Re: Setup IPSec to use specific outbound subnet address on WAN?
Dumb questions -just to be sure:
Did you specify that desired address as local-address in the peer definition?
Is that address actually really assigned to the router?
I have a couple of IPsec tunnels running here with multiple WAN addresses and they're running just fine as expected...
-Chris
Our tunnels are only working when using the pref-source from the WAN-subnet as peer address at both ends. How did you manage to pick any other subnet IP as the outbound address for the tunnel?
Last edited by Larsa on Thu Dec 07, 2017 2:15 pm, edited 1 time in total.
Re: Setup IPSec to use specific outbound subnet address on WAN?
Will check this when I'm back in the office.
-Chris
-Chris
Re: Setup IPSec to use specific outbound subnet address on WAN?
Not back in the office, but I have an idea to check in the mean time:
Do you have any masquerade rules configured in /ip firewall nat?
I could bet you have.
Masquerade always uses the lowest address on the interface, no matter what is defined beforehand.
Convert this rule to src-nat (and to-address to your desired address on that interface you wish to use for regular traffic) and then it should work.
-Chris
Do you have any masquerade rules configured in /ip firewall nat?
I could bet you have.
Masquerade always uses the lowest address on the interface, no matter what is defined beforehand.
Convert this rule to src-nat (and to-address to your desired address on that interface you wish to use for regular traffic) and then it should work.
-Chris
Re: Setup IPSec to use specific outbound subnet address on WAN?
Not back in the office, but I have an idea to check in the mean time:
Do you have any masquerade rules configured in /ip firewall nat?
I could bet you have.
Masquerade always uses the lowest address on the interface, no matter what is defined beforehand.
Convert this rule to src-nat (and to-address to your desired address on that interface you wish to use for regular traffic) and then it should work.
-Chris
We're using src-nat but I don't think it matters since you have to define "accept srcnat src.address dst.adress" as the first entry for the tunnel to disable any further NAT-translations.
Re: Setup IPSec to use specific outbound subnet address on WAN?
I wasn't talking about excluding the tunneled subnets from srcnat but about how outbound traffic is handled by the router - and this does matter.We're using src-nat but I don't think it matters since you have to define "accept srcnat src.address dst.adress" as the first entry for the tunnel to disable any further NAT-translations.
Anyway - I won't make it back to my desk before Monday, so I built a working config from scratch here with two routers I have lying around.
And I can confirm that it's 100% working.
This is router A
Code: Select all
/ip address
add address=172.17.17.1/24 interface=ether9 network=172.17.17.0
add address=172.17.17.2/24 interface=ether9 network=172.17.17.0
add address=172.17.18.1/24 interface=bridge2 network=172.17.18.0
/ip ipsec peer
add address=172.17.17.4/32 local-address=172.17.17.2 my-id=address:172.17.17.2 \
secret=test
/ip ipsec policy
add dst-address=172.17.19.0/24 sa-dst-address=172.17.17.4 sa-src-address=\
172.17.17.2 src-address=172.17.18.0/24 tunnel=yes
This is router B:
Code: Select all
/ip address
add address=172.17.17.3/24 interface=ether9 network=172.17.17.0
add address=172.17.17.4/24 interface=ether9 network=172.17.17.0
add address=172.17.19.1/24 interface=bridge2 network=172.17.19.0
/ip ipsec peer
add address=172.17.17.2/32 local-address=172.17.17.4 my-id=address:172.17.17.4 \
secret=test
/ip ipsec policy
add dst-address=172.17.18.0/24 sa-dst-address=172.17.17.2 sa-src-address=\
172.17.17.4 src-address=0.0.0.0/0 tunnel=yes
As you can see, on router B, it's perfectly established:
Code: Select all
[admin@routerB] > /ip ipsec remote-peers pr
Flags: R - responder, N - natt-peer
# ID STATE
0 established
[admin@routerB] > /ip ipsec installed-sa pr
Flags: A - AH, E - ESP
0 E spi=0x12CA5BF src-address=172.17.17.2 dst-address=172.17.17.4 state=mature
auth-algorithm=sha1 enc-algorithm=3des enc-key-size=192
auth-key="6e05dcf8e9dcaa9233b76962b5427ad1e109d1b7"
enc-key="8380b7f94995137fcf9d6ea021776e68888fd95e6832f2fa"
add-lifetime=24m/30m replay=128
1 E spi=0x5ACCAAD src-address=172.17.17.4 dst-address=172.17.17.2 state=mature
auth-algorithm=sha1 enc-algorithm=3des enc-key-size=192
auth-key="8856ab852815c05857b119dd3b2e70c705aae721"
enc-key="2fe96ffadcb2413f4c216f71a49110d10e22e2a457278258"
add-lifetime=24m/30m replay=128
So, this is a working IPsec tunnel between two routers with two addresses each on the IPsec-facing interface, peering each other through the higher IPs.
Hope, that helps.
-Chris
Re: Setup IPSec to use specific outbound subnet address on WAN?
Sorry, but I forgot to mention that the tunnel gets established but cannot pass any packets since the remote peer gets pref-source from the sending side as the return address i.e outbound address = pref-source. If possible, please enable logging for protocol 50 (ESP) and check for the same behavior.
Btw, did you manage to ping between the interfaces?
Thanks in advance!
Btw, did you manage to ping between the interfaces?
Thanks in advance!
Re: Setup IPSec to use specific outbound subnet address on WAN?
Sorry for the delay- I was a bit more than just busy.
So I tested everything again and it is definitely working and I am passing traffic through the tunnel.
What I noticed is that the tunnel breaks if one or both of the routers do not have a default route. That was new to me too.
-Chris
So I tested everything again and it is definitely working and I am passing traffic through the tunnel.
What I noticed is that the tunnel breaks if one or both of the routers do not have a default route. That was new to me too.
-Chris
Re: Setup IPSec to use specific outbound subnet address on WAN?
You need to have a route that matches your traffic. Normally the default route will do that.
Still I think you should re-consider using a GRE/IPsec tunnel instead of a direct IPsec tunnel.
Things will be much clearer in that configuration and it also allows extension e.g. with multiple subnets and routers.
Still I think you should re-consider using a GRE/IPsec tunnel instead of a direct IPsec tunnel.
Things will be much clearer in that configuration and it also allows extension e.g. with multiple subnets and routers.
Re: Setup IPSec to use specific outbound subnet address on WAN?
Now you mention it... that makes sense. Thanks.
And I second the proposal for GRE/IPsec
-Chris
And I second the proposal for GRE/IPsec
-Chris
Re: Setup IPSec to use specific outbound subnet address on WAN?
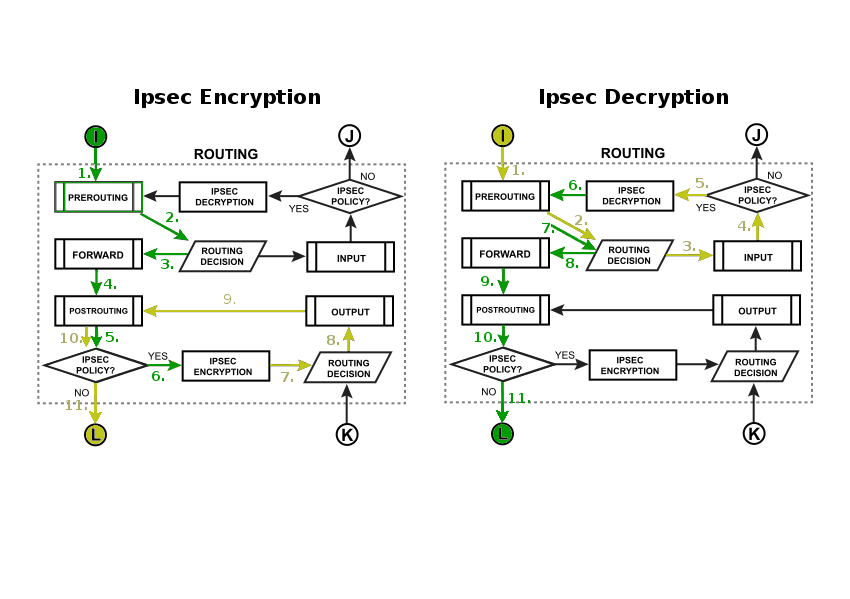
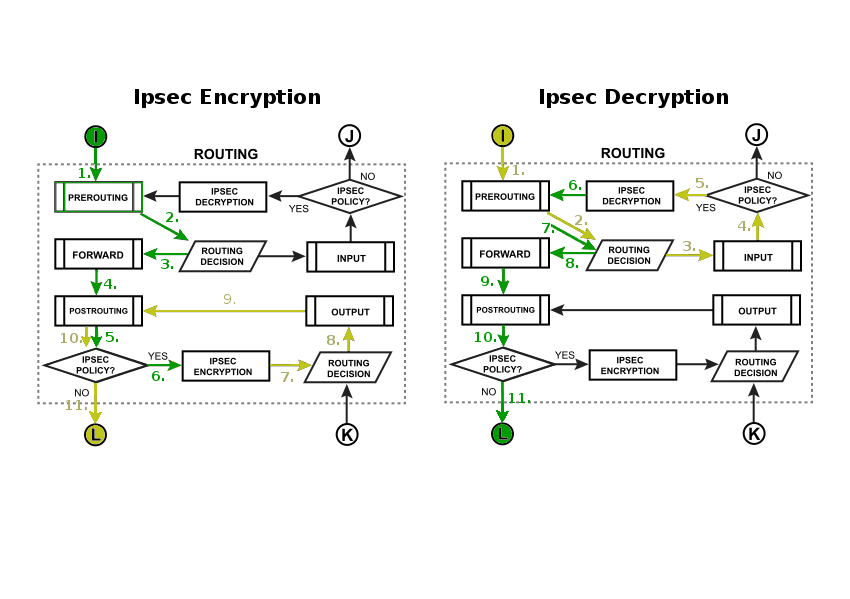
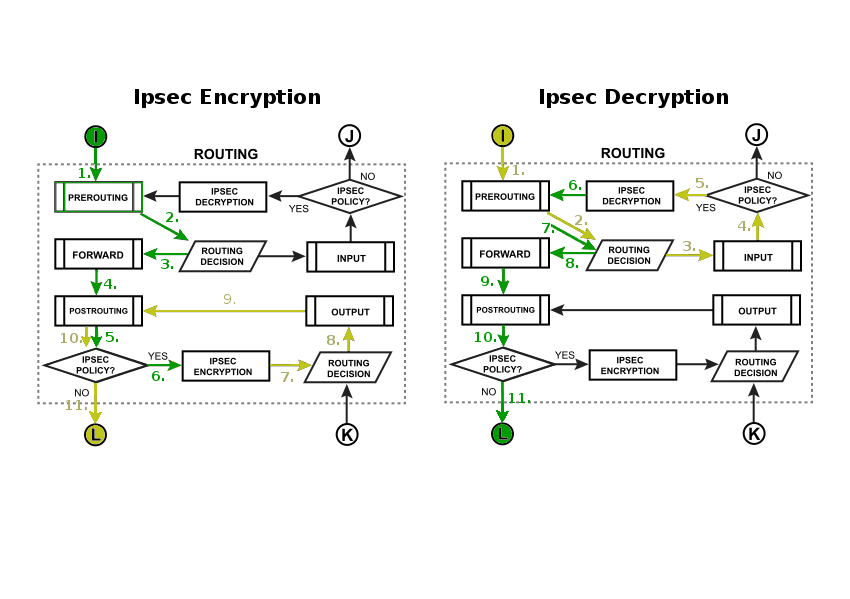
Packet flow diagram will illustrate why you need route for destination even if gateway of that route will not be used:
Re: Setup IPSec to use specific outbound subnet address on WAN?
Now you mention it... that makes sense. Thanks.
And I second the proposal for GRE/IPsec
-Chris
I concur, but even if you put GRE/L2PT on top of the tunnel you'll probably get the same issue with the outbound address as before...
Re: Setup IPSec to use specific outbound subnet address on WAN?
Packet flow diagram will illustrate why you need route for destination even if gateway of that route will not be used:
So if I understand it correcly, then the only way to set the outbound address of the tunnel is to control pref-src by for example:
- Define each ip address in the WAN subnet as /32 that automatically gets it's own routing path and pref source.
- Set a static route i.e "ip route dst-address=x.x.x.x/32 gateway=y.y.y.y pref-src=x.x.x.x"
Any advantage one has over the other?
Re: Setup IPSec to use specific outbound subnet address on WAN?
Sorry for the delay- I was a bit more than just busy.
So I tested everything again and it is definitely working and I am passing traffic through the tunnel.
What I noticed is that the tunnel breaks if one or both of the routers do not have a default route. That was new to me too.
-Chris
Chris, thanks for trying this out! It's nice to know we both get the same behavior. //Lars.
Re: Setup IPSec to use specific outbound subnet address on WAN? [SOLVED]
Don't do it that way!I concur, but even if you put GRE/L2PT on top of the tunnel you'll probably get the same issue with the outbound address as before...
Delete the IPsec Peer and Policy you have now, create a GRE interface, specify source and destination address (the public IPs of the routers) and set an IPsec secret.
Then put a /30 network on the GRE interfaces (e.g. 10.0.0.1/30 and 10.0.0.2/30) and route the networks on each side via that gateway.
Re: Setup IPSec to use specific outbound subnet address on WAN?
Don't do it that way!
Delete the IPsec Peer and Policy you have now, create a GRE interface, specify source and destination address (the public IPs of the routers) and set an IPsec secret.
Then put a /30 network on the GRE interfaces (e.g. 10.0.0.1/30 and 10.0.0.2/30) and route the networks on each side via that gateway.
Got it! GRE/IPsec seems far more easier than the other way around, thanks! Btw, is there any kind of dead peer detection you have to take into account in this case?
Re: Setup IPSec to use specific outbound subnet address on WAN?
dead peer detection should be enabled by default (interval 120 tries 5)
Re: Setup IPSec to use specific outbound subnet address on WAN?
dead peer detection should be enabled by default (interval 120 tries 5)
Normally, you set stuff like DPD and Lifetime using the ipsec peer config but what settings are used for the GRE dynamic IPSec tunnels? The GRE Wiki seems pretty brief (or actually completly empty) on this subject ...
Re: Setup IPSec to use specific outbound subnet address on WAN?
When you create and establish the tunnel, you will see the used Policy and Peer entries in the IPsec menu (read-only).
They use the proposal and policy template group named "default", which you can modify (before establishing the tunnel).
When you are not satisfied with the parameters and don't want to modify the defaults (e.g. because you have different tunnels
with different parameters) you can have a look at the created Policy and Peer entries, then remove the IPsec secret from the
GRE tunnel interface (so it becomes unencrypted) and then manually create policy and peer entries based on what you have
seen in the dynamically created entries (i.e. the same except what you want to have differently).
They use the proposal and policy template group named "default", which you can modify (before establishing the tunnel).
When you are not satisfied with the parameters and don't want to modify the defaults (e.g. because you have different tunnels
with different parameters) you can have a look at the created Policy and Peer entries, then remove the IPsec secret from the
GRE tunnel interface (so it becomes unencrypted) and then manually create policy and peer entries based on what you have
seen in the dynamically created entries (i.e. the same except what you want to have differently).
Re: Setup IPSec to use specific outbound subnet address on WAN?
Thanks for the thorough answer and hands-on guidance is always much appreciated as well!
Who is online
Users browsing this forum: Bing [Bot], pmcsill and 105 guests



