We have started replacing older routers running OpenBSD for Routerboard RB750GL.
Smaller, neater, less that can break.
But one of the things when using OpenBSD on all nodes, was that is more or less just worked as intended, without much hassle.
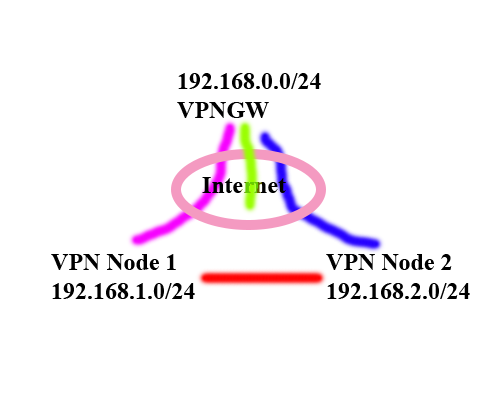
I have simplified the setup below, there are many many more nodes in reality.
VPN GW
----------
OpenBSD
WAN: 1.1.1.1
LAN: 192.168.0.1
VPN Node 1
----------
OpenBSD
WAN: 2.2.2.2
LAN: 192.168.1.1
VPN Node 2
----------
RouterBoard RB750GL
WAN: 3.3.3.3
LAN: 192.168.2.1
Each Node is connected to the GW.
Node 1 <-> GW <-> Node 2
The SRC. Address of each node is its Lan/24, and the DST. Adress is 0.0.0.0/0, so everything is routed thru the IPSEC.
The issue is that when there where no Routerboards There was also another link.
Node 1 <-> Node 2
So traffic between 192.168.1.0/24 <-> 192.168.2.0/24 used this link, and did not go over the GW.
Easing the load when branches speak.
But with multiple Policies and require/uniqe configuration on the policies, different priorites, the second connection for the inter node connection is never established.
Since of course 0.0.0.0/0 covers the address space, why should it.
And even if I used 192.168.0.0/16 instead of 0.0.0.0/0 the same problem would be true.
Each Policy/peer/proposal on its own, workes as intended. But togehter only the connection to the GW is used.
Tehre are also NAT rules to bypass Masquerade for each policy.
Any ideas / sugestions?
For testing purposes I have setup Two RB750GL connected to a OpenBSD GW, to test solutions on, I have attached a compact export of these.
External IPs Redacted, but the PSK is in there, if you want to go hunting