Could be a case of cheap Android trash?
To help eliminate some possibilities,
Have you tried removing TP-Link switch from the equation and connect directly to MT?
Have you tried disconnecting connection from TV and connect to another device, such as laptop. Does it experience same issue?
1. Yes i tryed first without switch, Android Box get IP just a first time, and works until box is power ON. When i power OFF, and power ON after some time, it dont get IP from DHCP anymore.
2. Yes other devices works normaly. Its brand new hAP AX3 old just one week.
https://androidpctv.com/review-mecool-m8s-pro-l/ is the Android TV Box i use.
Sounds strange. However without your configuration, we would be guessing. Please post your configuration.
To export and paste your configuration (and I'm assuming you are using WebFig or Winbox), open a terminal window, and type (without the quotes) "/export hide-sensitive file=any-filename-you-wish". Then open the files section and right click on the filename you created and select download in order to download the file to your computer. It will be a text file with whatever name you saved to with an extension of .rsc. Suggest you then open the .rsc file in your favorite text editor and redact any sensitive information. Then in your message here, click the code display icon in the toolbar above the text entry (the code display icon is the 7th one from the left and looks like a square with a blob in the middle). Then paste the text from the file in between the two code words in brackets.
Here is it:
# jun/01/2023 10:41:22 by RouterOS 7.8
# software id = MGL0-4L4W
#
# model = C53UiG+5HPaxD2HPaxD
# serial number = removed-private
/interface bridge
add admin-mac=48:A9:8A:BA:EF:XX auto-mac=no comment=defconf name=bridge
/interface ethernet
set [ find default-name=ether1 ] name=WAN1
set [ find default-name=ether2 ] name=WAN2
/interface wifiwave2
set [ find default-name=wifi1 ] channel.band=5ghz-ax .skip-dfs-channels=\
10min-cac .width=20/40/80mhz configuration.mode=ap .ssid=MikroTik-5G \
disabled=no security.authentication-types=wpa-psk,wpa2-psk
set [ find default-name=wifi2 ] channel.band=2ghz-ax .skip-dfs-channels=\
10min-cac .width=20mhz configuration.mode=ap .ssid=MikroTik-2G disabled=\
no security.authentication-types=wpa-psk,wpa2-psk
/interface list
add comment=defconf name=WAN
add comment=defconf name=LAN
/ip pool
add name=default-dhcp ranges=192.168.88.10-192.168.88.254
/ip dhcp-server
add address-pool=default-dhcp interface=bridge name=defconf
/routing table
add disabled=no fib name=WAN1
add disabled=no fib name=WAN2
/interface bridge port
add bridge=bridge comment=defconf interface=ether3
add bridge=bridge comment=defconf interface=ether4
add bridge=bridge comment=defconf interface=ether5
add bridge=bridge comment=defconf interface=wifi1
add bridge=bridge comment=defconf interface=wifi2
/ip neighbor discovery-settings
set discover-interface-list=LAN
/interface list member
add comment=defconf interface=bridge list=LAN
add comment=defconf interface=WAN1 list=WAN
/ip address
add address=192.168.88.1/24 comment=defconf interface=bridge network=\
192.168.88.0
/ip cloud
set ddns-enabled=yes ddns-update-interval=30m
/ip dhcp-client
add add-default-route=no comment=defconf interface=WAN1
add add-default-route=no interface=WAN2
/ip dhcp-server lease
add address=192.168.88.12 client-id=1:9c:14:63:7e:91:95 mac-address=\
9C:14:63:7E:91:XX server=defconf
add address=192.168.88.25 client-id=1:d0:76:58:10:60:d5 lease-time=5m \
mac-address=D0:76:58:10:60:XX server=defconf
/ip dhcp-server network
add address=192.168.88.0/24 comment=defconf dns-server=192.168.88.1 gateway=\
192.168.88.1
/ip dns
set allow-remote-requests=yes
/ip dns static
add address=192.168.88.1 comment=defconf name=router.lan
/ip firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input dst-port=8291 protocol=tcp
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment=\
"defconf: accept to local loopback (for CAPsMAN)" dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" \
in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" \
ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" \
ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related hw-offload=yes
add action=accept chain=forward comment=\
"defconf: accept established,related, untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat \
connection-state=new in-interface-list=WAN
/ip firewall mangle
add action=accept chain=prerouting dst-address=192.168.1.0/24 in-interface=\
bridge
add action=accept chain=prerouting dst-address=192.168.99.0/24 in-interface=\
bridge
add action=mark-connection chain=prerouting connection-mark=no-mark \
in-interface=WAN1 new-connection-mark=WAN1_conn passthrough=yes
add action=mark-connection chain=prerouting connection-mark=no-mark \
in-interface=WAN2 new-connection-mark=WAN2_conn passthrough=yes
add action=mark-connection chain=prerouting connection-mark=no-mark \
dst-address-type=!local in-interface=bridge new-connection-mark=WAN1_conn \
passthrough=yes per-connection-classifier=both-addresses:2/0
add action=mark-connection chain=prerouting connection-mark=no-mark \
dst-address-type=!local in-interface=bridge new-connection-mark=WAN2_conn \
passthrough=yes per-connection-classifier=both-addresses:2/1
add action=mark-routing chain=prerouting connection-mark=WAN1_conn \
in-interface=bridge new-routing-mark=WAN1 passthrough=yes
add action=mark-routing chain=prerouting connection-mark=WAN2_conn \
in-interface=bridge new-routing-mark=WAN2 passthrough=yes
add action=mark-routing chain=output connection-mark=WAN1_conn \
new-routing-mark=WAN1 passthrough=yes
add action=mark-routing chain=output connection-mark=WAN2_conn \
new-routing-mark=WAN2 passthrough=yes
/ip firewall nat
add action=masquerade chain=srcnat out-interface=WAN1
add action=masquerade chain=srcnat out-interface=WAN2
/ip route
add check-gateway=ping disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.1.1 pref-src="" routing-table=WAN1 scope=30 suppress-hw-offload=\
no target-scope=10
add check-gateway=ping disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.99.1 pref-src="" routing-table=WAN2 scope=30 suppress-hw-offload=\
no target-scope=10
add check-gateway=ping disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.1.1 pref-src="" routing-table=WAN1 scope=30 suppress-hw-offload=\
no target-scope=11
add check-gateway=ping disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
192.168.99.1 pref-src="" routing-table=WAN2 scope=30 suppress-hw-offload=\
no target-scope=11
/ip service
set telnet disabled=yes
set ftp disabled=yes
set www disabled=yes
set ssh disabled=yes
set api-ssl disabled=yes
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only " list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
/ipv6 firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" port=\
33434-33534 protocol=udp
add action=accept chain=input comment=\
"defconf: accept DHCPv6-Client prefix delegation." dst-port=546 protocol=\
udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 \
protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=input comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=\
!LAN
add action=accept chain=forward comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop packets with bad src ipv6" src-address-list=bad_ipv6
add action=drop chain=forward comment=\
"defconf: drop packets with bad dst ipv6" dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" \
hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=\
500,4500 protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=forward comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=\
!LAN
/system clock
set time-zone-name=Europe/Skopje
/system ntp client
set enabled=yes
/system ntp client servers
add address=0.europe.pool.ntp.org
add address=1.europe.pool.ntp.org
/tool mac-server
set allowed-interface-list=LAN
192.168.88.25 is fixed IP for Android TV box i set.
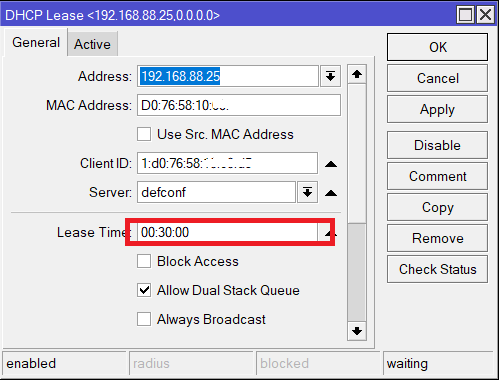
Try changing the lease-time setting in the DHCP server to 00:30:00 (or 30m). It's possible the Android box doesn't like the short lease time.
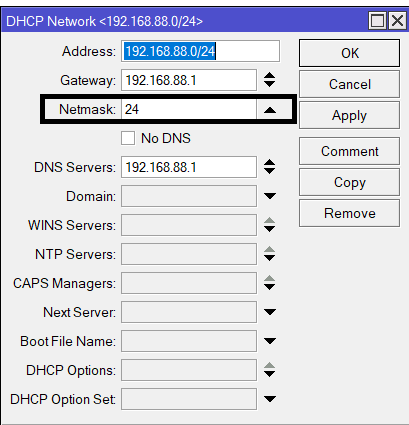
Also, under DHCP Server > Networks set the netmask for your network to 24 (or what your subnet CIDR is) – even though it's already specified in the DHCP network address= line. I've seen some devices need that set for some unknown reason (e.g. it should be inferred from the address, but not always it seems)
Set 30 min lease time just for that static IP adress 192.168.88.25 . No need to set 30 min lease time for entire DHCP server.
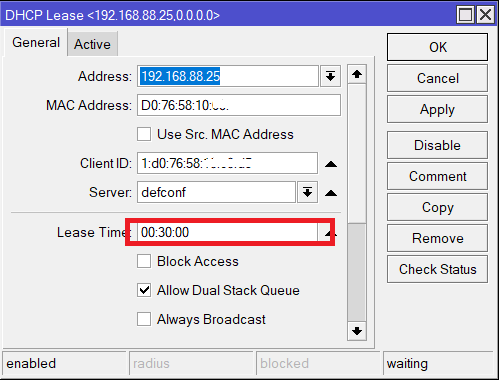
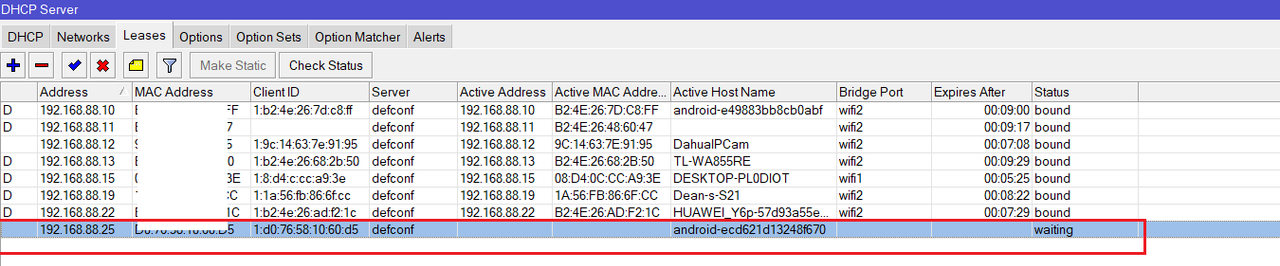
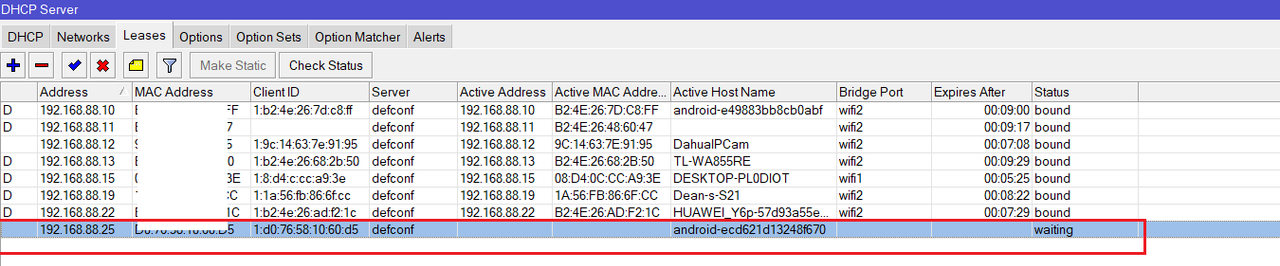
and this is after Android Box is powered ON. Still stuck on
waiting status