My config just represents how far all kind of HowTo's have gotten me - confused.
Which as previously said I mostly blame on no info which ROS Version and HW said HowTo were referring to

anyways I have been trying to pick up on your advice as much as I could before everything broke to hell - again. First of all I know my FW rules are the #1 mess out there but I'm trying to figure out most rules ahead of removing that one rule that allows through most of the traffic currently, I promise I'll work on it but first things first, here's the current config:
# mar/30/2023 17:40:12 by RouterOS 7.8
# software id = PNTF-DUHH
#
# model = RB4011iGS+5HacQ2HnD
# serial number =
/interface bridge
add frame-types=admit-only-vlan-tagged name=BR1 vlan-filtering=yes
add admin-mac=xx:xx:xx:xx:xx:xx auto-mac=no comment=defconf name=bridge
/interface wireless
set [ find default-name=wlan1 ] band=5ghz-a/n/ac channel-width=\
20/40/80mhz-XXXX distance=indoors frequency=auto installation=indoor \
mode=ap-bridge secondary-frequency=auto ssid=MikroTik-4B246C \
wireless-protocol=802.11
set [ find default-name=wlan2 ] band=2ghz-b/g/n channel-width=20/40mhz-XX \
distance=indoors frequency=auto installation=indoor mode=ap-bridge ssid=\
MikroTik-B39B25 wireless-protocol=802.11
/interface vlan
add interface=BR1 name=Arlo_VLAN vlan-id=30
add interface=BR1 name=BASE_VLAN vlan-id=188
add interface=BR1 name=Alexa_VLAN vlan-id=20
add interface=BR1 name=Sehr_VLAN vlan-id=60
add interface=BR1 name=Gscht_VLAN vlan-id=120
add interface=BR1 name=Hue_VLAN vlan-id=40
add interface=BR1 name=IoTRest_VLAN vlan-id=50
/interface list
add comment=defconf name=WAN
add comment=defconf name=LAN
add name=VLAN
add name=BASE
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/ip pool
add name=Alexa_POOL ranges=192.168.20.2-192.168.20.250
add name=Arlo_POOL ranges=192.168.30.2-192.168.30.250
add name=Hue_POOL ranges=192.168.40.2-192.168.40.250
add name=IoTRest_POOL ranges=192.168.50.2-192.168.50.250
add name=Sehr_POOL ranges=192.168.60.2-192.168.60.250
add name=Gscht_POOL ranges=192.168.120.2-192.168.120.250
add name=BASE_POOL ranges=192.168.188.2-192.168.188.250
/ip dhcp-server
add add-arp=yes address-pool=Alexa_POOL interface=Alexa_VLAN name=\
Alexa_DHCP
add add-arp=yes address-pool=Arlo_POOL interface=Arlo_VLAN name=Arlo_DHCP
add add-arp=yes address-pool=Hue_POOL interface=Hue_VLAN name=Hue_DHCP
add add-arp=yes address-pool=IoTRest_POOL interface=IoTRest_VLAN name=\
IoTRest_DHCP
add add-arp=yes address-pool=Sehr_POOL interface=Sehr_VLAN name=\
Sehr_DHCP
add add-arp=yes address-pool=Gscht_POOL interface=Gscht_VLAN name=Gscht_DHCP
add add-arp=yes address-pool=BASE_POOL interface=BASE_VLAN name=BASE_DHCP
/port
set 0 name=serial0
set 1 name=serial1
/interface bridge port
add bridge=BR1 comment=defconf frame-types=\
admit-only-untagged-and-priority-tagged interface=ether2 pvid=188
add bridge=BR1 frame-types=admit-only-untagged-and-priority-tagged interface=\
ether3 pvid=60
add bridge=BR1 frame-types=admit-only-untagged-and-priority-tagged interface=\
ether4 pvid=60
add bridge=BR1 frame-types=admit-only-untagged-and-priority-tagged interface=\
ether5 pvid=60
add bridge=BR1 frame-types=admit-only-untagged-and-priority-tagged interface=\
ether6 pvid=60
add bridge=BR1 frame-types=admit-only-untagged-and-priority-tagged interface=\
ether7 pvid=60
add bridge=BR1 frame-types=admit-only-untagged-and-priority-tagged interface=\
ether8 pvid=60
add bridge=BR1 frame-types=admit-only-untagged-and-priority-tagged interface=\
ether9 pvid=60
add bridge=BR1 frame-types=admit-only-untagged-and-priority-tagged interface=\
ether10 pvid=60
add bridge=BR1 frame-types=admit-only-vlan-tagged interface=sfp-sfpplus1 \
pvid=188
/ip neighbor discovery-settings
set discover-interface-list=BASE
/interface bridge vlan
add bridge=BR1 tagged=BR1,sfp-sfpplus1 vlan-ids=20
add bridge=BR1 tagged=BR1,sfp-sfpplus1 vlan-ids=30
add bridge=BR1 tagged=BR1,sfp-sfpplus1 vlan-ids=40
add bridge=BR1 tagged=BR1,sfp-sfpplus1 vlan-ids=50
add bridge=BR1 tagged=BR1,sfp-sfpplus1 vlan-ids=60
add bridge=BR1 tagged=BR1,sfp-sfpplus1 vlan-ids=120
add bridge=BR1 tagged=BR1,sfp-sfpplus1 vlan-ids=188
/interface list member
add comment=defconf interface=ether1 list=WAN
add interface=Alexa_VLAN list=VLAN
add interface=Arlo_VLAN list=VLAN
add interface=Hue_VLAN list=VLAN
add interface=IoTRest_VLAN list=VLAN
add interface=Sehr_VLAN list=VLAN
add interface=BASE_VLAN list=BASE
/ip address
add address=192.168.20.1/24 interface=Alexa_VLAN network=192.168.20.0
add address=192.168.30.1/24 interface=Arlo_VLAN network=192.168.30.0
add address=192.168.40.1/24 interface=Hue_VLAN network=192.168.40.0
add address=192.168.50.1/24 interface=IoTRest_VLAN network=192.168.50.0
add address=192.168.60.1/24 interface=Sehr_VLAN network=192.168.60.0
add address=192.168.120.1/24 interface=Gscht_VLAN network=192.168.120.0
add address=192.168.188.1/24 interface=BASE_VLAN network=192.168.188.0
/ip cloud
set ddns-enabled=yes
/ip dhcp-client
add comment=defconf interface=ether1
/ip dhcp-server network
add address=192.168.20.0/24 dns-server=1.1.1.1,1.0.0.1 gateway=192.168.20.1
add address=192.168.30.0/24 dns-server=1.1.1.1,1.0.0.1 gateway=192.168.30.1
add address=192.168.40.0/24 dns-server=1.1.1.1,1.0.0.1 gateway=192.168.40.1
add address=192.168.50.0/24 dns-server=1.1.1.1,1.0.0.1 gateway=192.168.50.1
add address=192.168.60.0/24 dns-server=1.1.1.1,1.0.0.1 gateway=192.168.60.1
add address=192.168.120.0/24 dns-server=1.1.1.1,1.0.0.1 gateway=192.168.120.1
add address=192.168.188.0/24 dns-server=1.1.1.1,1.0.0.1 gateway=192.168.188.1
/ip dns
set allow-remote-requests=yes
/ip dns static
add address=192.168.88.1 comment=defconf name=router.lan
/ip firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment=\
"defconf: accept to local loopback (for CAPsMAN)" dst-address=127.0.0.1
add action=accept chain=forward comment="defconf: accept in ipsec policy" \
ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" \
ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related hw-offload=yes
add action=accept chain=forward comment=\
"defconf: accept established,related, untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat \
connection-state=new in-interface-list=WAN
add action=accept chain=input comment="Allow Estab & Related" \
connection-state=established,related
add action=accept chain=input comment="Allow Base_Vlan Full Access" \
in-interface=BASE_VLAN
add action=accept chain=input in-interface=bridge
add action=accept chain=forward comment="Allow Estab & Related" \
connection-state=established,related
add action=accept chain=forward comment="VLAN Internet Access only" \
connection-state=new in-interface-list=VLAN out-interface-list=WAN
add action=accept chain=forward connection-state=new in-interface-list=BASE \
out-interface-list=VLAN
add action=accept chain=forward connection-state=new in-interface=\
Alexa_VLAN out-interface=Arlo_VLAN
add action=accept chain=forward in-interface=BASE_VLAN out-interface-list=WAN
add action=accept chain=forward in-interface=Alexa_VLAN out-interface=\
Hue_VLAN
add action=accept chain=forward in-interface=IoTRest_VLAN out-interface=\
Hue_VLAN
add action=accept chain=forward in-interface=IoTRest_VLAN out-interface=\
Sehr_VLAN
add action=accept chain=forward in-interface=Hue_VLAN out-interface=BASE_VLAN
add action=accept chain=forward in-interface=BASE_VLAN out-interface=Hue_VLAN
add action=accept chain=forward in-interface=BASE_VLAN out-interface=\
Sehr_VLAN
add action=accept chain=forward in-interface=BASE_VLAN out-interface=\
IoTRest_VLAN
add action=drop chain=input
/ip firewall nat
add action=masquerade chain=srcnat comment="defconf: masquerade" \
ipsec-policy=out,none out-interface-list=WAN
add action=masquerade chain=srcnat comment="Default masquerade" \
out-interface-list=WAN
/ip firewall service-port
set rtsp disabled=no
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only " list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
/ipv6 firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" port=\
33434-33534 protocol=udp
add action=accept chain=input comment=\
"defconf: accept DHCPv6-Client prefix delegation." dst-port=546 protocol=\
udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 \
protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=input comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=\
!LAN
add action=accept chain=forward comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"defconf: drop packets with bad src ipv6" src-address-list=bad_ipv6
add action=drop chain=forward comment=\
"defconf: drop packets with bad dst ipv6" dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" \
hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=\
500,4500 protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=forward comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=\
!LAN
/system clock
set time-zone-name=Europe/Berlin
/system identity
set name=r00ter
/system leds
add interface=wlan2 leds="wlan2_signal1-led,wlan2_signal2-led,wlan2_signal3-le\
d,wlan2_signal4-led,wlan2_signal5-led" type=wireless-signal-strength
add interface=wlan2 leds=wlan2_tx-led type=interface-transmit
add interface=wlan2 leds=wlan2_rx-led type=interface-receive
/tool mac-server
set allowed-interface-list=BASE
/tool mac-server mac-winbox
set allowed-interface-list=BASE
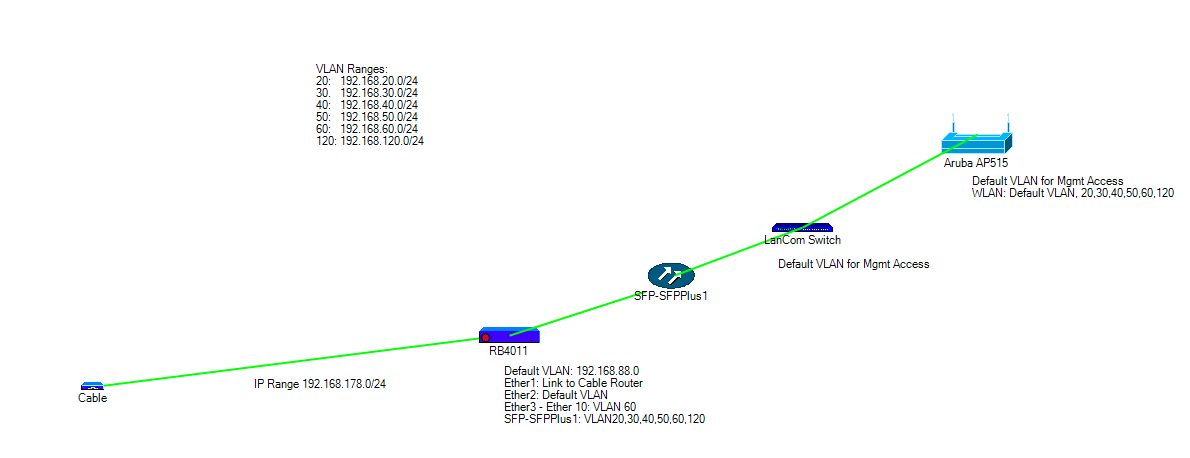
on the LanCom Switch Port 9 is the SFP+ Port which is the connection to the RB4011 via sfp-sfpplus1 interface. it's set up as Trunk port (C-Port) and Egress is set to Tag all traffic, base PVID is set to 188.
Ports 6 -8 are configured as Hybrid ports, S-Custom Port where S-Custom is set to 8100 and it's set to untag base PVID which is set to VLAN 188. Here are 2x Aruba AP515 and an AP505 connected which serve Wifi.
Ingress filtering is added on Port 6 -8 and it's added on Port 9 by trunk choice on the port type selection on the LanCom switch, too.
What I don't get is an DHCP offer on either the switch or the Access Points. I don't get any DHCP offer on anything that's connected via sfp-sfpplus1 except for the switch management interface, I do have VLAN accessibility on the switch as I can configure any access port / VLAN and if using proper manual IP settings I can at least access local resources but the gateway IP of the RB4011 seems unreachable most of the time regardless of in which VLAN I place my client.
I have tried a full config reset on the switch and left out any configuration afterwards asides getting a management interface running on VLAN 188 and above mentioned port configuration for uplink between switch and rb4011 and link between switch and Access Points but problem didn't change at all: No DHCP lease offer and destination unreachable / packet loss gateway when trying to ping it while on manual IP config. I did add my switch as DHCP Relay and pointed it to 192.168.188.1 and I do see on statistics that traffic in that regard does seem to happen without loss so I don't see how the switch would be blocking DHCP offers being sent via sfp-sfpplus1 and it has been working before so the only place I can imagine my screw up is the RB4011 config.
I blame my rb4011 for this but I can't see how this happened exactly so any pointers in my config to potentially get rid of this asap would be awesome.
I do have a big stack of open issues to chew through for the forseeable future too but currently it's we have no working Wifi at all which is most concerning and any help is appreciated.
I could imagine some issues being related to me trying to get IGMP / DHCP Snooping and relay to work across the switch and RB4011 but I've reset switch config completely and removed most of it on the RB4011 config, too in order to try to rule that out as reason for my troubles with DHCP offers and unreachable gateway if an offer actually was received.