comrades,
is there a simple and understandable step-by-step manual, how to setup Mikrotik (7.1.1) as WireGuard client ?
Re: Mikrotik as WireGuard client
MT does NOT equal simple.
https://help.mikrotik.com/docs/display/ROS/WireGuard
viewtopic.php?t=174417
https://help.mikrotik.com/docs/display/ROS/WireGuard
viewtopic.php?t=174417
Re: Mikrotik as WireGuard client
and how it is possible to completely wrap all traffic from the local network into this tunnel ?
Re: Mikrotik as WireGuard client
Simple.
Set allowed addresses to 0.0.0.0/0
Everything will go down the drain... errrrmm the tunnel.
Set allowed addresses to 0.0.0.0/0
Everything will go down the drain... errrrmm the tunnel.
Re: Mikrotik as WireGuard client
RouterOS doesn't automatically add routes based on allowed addresses.
Configuration depends on your exact needs and other details. If you want to route everything through tunnel, with no fallback, check this (if you have static config and not dhcp, you don't need lease script):
viewtopic.php?p=897582#p897582
There can be different variations, e.g. if you'd want to use WG only when available and fall back to using your regular connection, if only selected devices from LAN should use tunnel, if server uses hostname that may be dynamic, etc.
Configuration depends on your exact needs and other details. If you want to route everything through tunnel, with no fallback, check this (if you have static config and not dhcp, you don't need lease script):
viewtopic.php?p=897582#p897582
There can be different variations, e.g. if you'd want to use WG only when available and fall back to using your regular connection, if only selected devices from LAN should use tunnel, if server uses hostname that may be dynamic, etc.
Re: Mikrotik as WireGuard client
actually yes, I have DHCP on the external interface (Internet)if you have static config and not dhcp
if you don't mind, I would like to ask: how and what does it change?
Re: Mikrotik as WireGuard client
Check the config in other thread. One part of it is a route that needs to be updated if router has dynamic address, so it's done using dhcp lease script. If there was static config, no script would be needed. Even with dhcp it would be possible without script, but at that time I simply liked this way. It's what RouterOS does, it allows you to solve things using different ways.
Re: Mikrotik as WireGuard client
That is a loaded question, it depends WHERE you mean.and how it is possible to completely wrap all traffic from the local network into this tunnel ?
For example I have a router acting as a client and I have a router acting as a server.
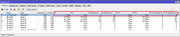
Case1: To ensure a subnet on the client router is used for all traffic I create a route rule.
dst 0.0.0.0/0 gw=wg interface Table=vpntunnel
Where the route rule establishes
the source subnet, the action of lookup only in table, the table selected is vpntunnel.
Case2: Now that traffic has reached the Server router wg interface.
What you do depends on the firewall rule set.
If you have the default rule, only WAN non-dst traffic is blocked and the router will move the tunnel traffic to the internet...........
If you have a block all rule then you have some choices to make.
a. add the WG-INTERFACE to the LAN as an interface list member and thus a typical LAN to WAN rule will include/allow such traffic.
b. create another firewall forward chain rule in-interface=wg interface out-interface-list=WAN
Note: the same thinking applies for example if the WG tunnel is coming from a smart phone!
Case 3: This time lets say you want to be able to use the wireguard from your smartphone to manage the router.
Well with the default rule on the input chain stating block all not from LAN then you have to make adjustments
a. add wg interface to LAN interface to gain access on input chain
b. add wg interface to MANAGMENT or BASE interface if no specific LAN rule exists (LAn users should only get dns access anyway).
c. create a specific rule in-input=wg interface accept etc...
@sob As I stated, LOOK MA NO HANDS - no IP addresses (for wg) were harmed or used in this config