what am i doing wrong?
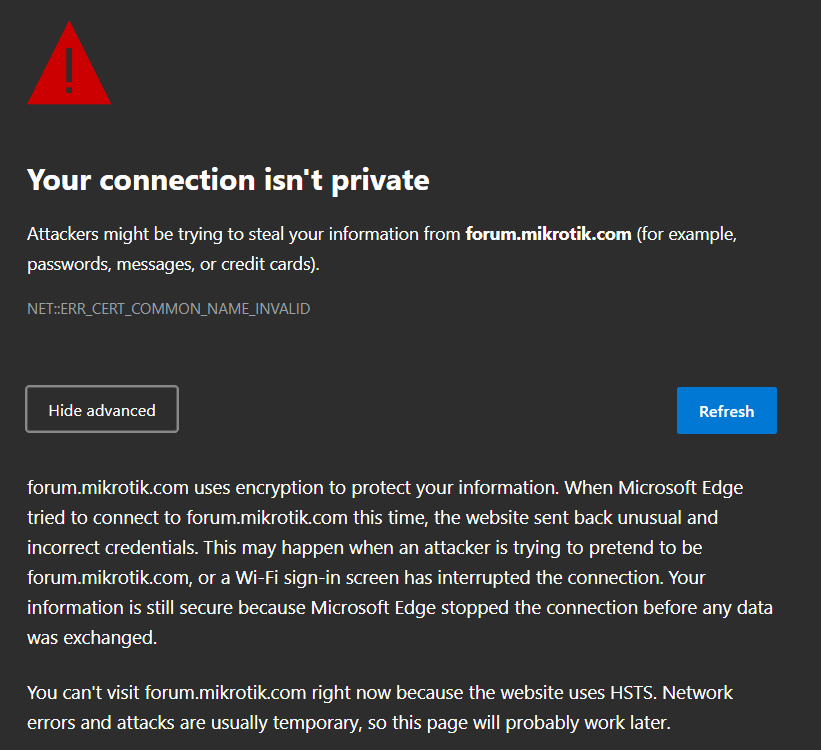
I have been using a mikrotik LHG 5 in the last 2 years as the main way to access the internet (PTMP). About 6 months ago I began receiving TLS errors on all my browsers on all websites (even google). and after 30 seconds to 5 minutes, it was ok and i had secure access to the websites. So, every now and then i needed to wait and refresh until I had the secure connection.
So, after logging into the LHG 5 (first experience with a mikrotik device) and spending a day or two tinkering in the GUI, I searched the default firewall and added the rules, and the problem went away for the next 3 months. After 3 months the problem was back.
I think i need to note that:
- All my windows devices have this problem.
- I use the same computer with ADSL and LTE internet with no TLS problems.
- yesterday I changed my ISP and now I'm connected to another tower, another direction and another ISP but same problem.
- while using a VPN (any protocol) on the computer, the problem goes away.
- since the ISP has the login credentials to the LHG 5, I added another router (hAP lite) between my devices and the LHG 5 but the problem still there.
- I turned off all of the IOT devices (smart lamps and plugs) for a while but the problem was there.
- my neighbor uses the same ISP with a LHG 5 and does not have this problem.
- syncing the computers time with NTP server does not help
- my ISP doesn't care to help; in my country this is normal. They told me to whenever this happens choose to continue with HTTP.
LHG 5 export:
Code: Select all
# nov/05/2022 10:15:14 by RouterOS 6.49.7
# software id = BBPZ-T9Z2
#
# model = RouterBOARD LHG 5nD
# serial number = **********
/interface wireless
set [ find default-name=wlan1 ] band=5ghz-a/n channel-width=20/40mhz-Ce country=no_country_set disabled=no frequency=5240 frequency-mode=superchannel mode=station-bridge scan-list=5240 ssid=\
1009416CT11-**********
/interface pppoe-client
add add-default-route=yes disabled=no interface=wlan1 name=pppoe-out1 use-peer-dns=yes user=**********
/interface list
add name=WAN
add name=LAN
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/ip neighbor discovery-settings
set discover-interface-list=!dynamic
/interface list member
add interface=pppoe-out1 list=WAN
add list=LAN
/ip address
add address=10.10.1.10/24 interface=ether1 network=10.10.1.0
/ip cloud
set update-time=no
/ip firewall filter
add action=accept chain=input comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=invalid
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment="defconf: accept to local loopback (for CAPsMAN)" dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" connection-state=established,related
add action=accept chain=forward comment="defconf: accept established,related, untracked" connection-state=established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" connection-state=invalid
add action=drop chain=forward comment="defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat connection-state=new in-interface-list=WAN
/ip firewall nat
add action=masquerade chain=srcnat
/ip service
set telnet disabled=yes
set ftp disabled=yes
set ssh disabled=yes
set api disabled=yes
set api-ssl disabled=yes
/system clock
set time-zone-autodetect=no time-zone-name=Asia/Tehran
/system identity
set name=**********
/tool mac-server
set allowed-interface-list=none
Code: Select all
# nov/05/2022 22:32:09 by RouterOS 7.5
# software id = C4NI-PF5J
#
# model = RB941-2nD
# serial number = **********
/interface pwr-line
set [ find default-name=pwr-line1 ] disabled=yes
/interface bridge
add admin-mac=08:55:31:A0:6A:7C auto-mac=no comment=defconf name=bridge
/interface ethernet
set [ find default-name=ether1 ] comment="ISP1 _PTMP _LHG5"
set [ find default-name=ether2 ] comment="ISP2 _LTE _DWRM921"
set [ find default-name=ether3 ] comment="wAC _GWN7615"
set [ find default-name=ether4 ] comment="HomeA _RPI"
/interface wireless
set [ find default-name=wlan1 ] band=2ghz-b/g/n channel-width=20/40mhz-XX \
distance=indoors frequency=auto installation=indoor mode=ap-bridge ssid=\
********** wireless-protocol=802.11
/interface list
add comment=defconf name=WAN
add comment=defconf name=LAN
/interface wireless security-profiles
set [ find default=yes ] supplicant-identity=MikroTik
/ip pool
add name=dpool ranges=10.10.10.100-10.10.10.200
add name=dhcp_pool2 ranges=10.10.1.1,10.10.1.11-10.10.1.254
add name=dhcp_pool3 ranges=10.10.10.100-10.10.10.199
/ip dhcp-server
add address-pool=dhcp_pool3 interface=bridge name=dhcp2
/routing ospf instance
add disabled=no name=default-v2
/routing ospf area
add disabled=yes instance=default-v2 name=backbone-v2
/interface bridge port
add bridge=bridge comment=defconf disabled=yes ingress-filtering=no interface=\
ether2
add bridge=bridge comment=defconf ingress-filtering=no interface=ether3
add bridge=bridge comment=defconf ingress-filtering=no interface=ether4
add bridge=bridge comment=defconf disabled=yes ingress-filtering=no interface=\
pwr-line1
add bridge=bridge comment=defconf disabled=yes ingress-filtering=no interface=\
wlan1
/ip neighbor discovery-settings
set discover-interface-list=LAN
/ip settings
set max-neighbor-entries=8192
/ipv6 settings
set disable-ipv6=yes max-neighbor-entries=8192
/interface list member
add comment=defconf interface=bridge list=LAN
add comment=defconf interface=ether1 list=WAN
/interface ovpn-server server
set auth=sha1,md5
/ip address
add address=10.10.10.1/24 interface=bridge network=10.10.10.0
add address=10.10.1.1/24 interface=ether1 network=10.10.1.0
add address=10.10.2.1/24 interface=ether2 network=10.10.2.0
/ip dhcp-client
add comment=defconf interface=ether1
/ip dhcp-server network
add address=10.10.1.0/24 dns-server=9.9.9.9,5.200.200.200 gateway=10.10.1.10
add address=10.10.10.0/24 dns-server=9.9.9.9,5.200.200.200 gateway=10.10.10.1
/ip dns
set allow-remote-requests=yes
/ip dns static
add address=192.168.88.1 comment=defconf name=router.lan
/ip firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment=\
"defconf: accept to local loopback (for CAPsMAN)" dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" \
in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" \
ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" \
ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related hw-offload=yes
add action=accept chain=forward comment=\
"defconf: accept established,related, untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" connection-state=\
invalid
add action=drop chain=forward comment="defconf: drop all from WAN not DSTNATed" \
connection-nat-state=!dstnat connection-state=new in-interface-list=WAN
/ip firewall nat
add action=masquerade chain=srcnat comment="defconf: masquerade" ipsec-policy=\
out,none out-interface-list=WAN
add action=masquerade chain=srcnat out-interface=ether2
/ip route
add comment=ISP1 disabled=no distance=1 dst-address=0.0.0.0/0 gateway=\
10.10.1.10 pref-src="" routing-table=main scope=30 suppress-hw-offload=no \
target-scope=10
add comment=LTE disabled=no distance=2 dst-address=0.0.0.0/0 gateway=10.10.2.10 \
pref-src="" routing-table=main scope=30 suppress-hw-offload=no \
target-scope=10
/ip service
set telnet disabled=yes
set ftp disabled=yes
set www disabled=yes
set ssh disabled=yes
set api disabled=yes
set api-ssl disabled=yes
/ip ssh
set strong-crypto=yes
/system clock
set time-zone-autodetect=no time-zone-name=Asia/Tehran
/system identity
set name=Home
/tool mac-server
set allowed-interface-list=none
/tool mac-server mac-winbox
set allowed-interface-list=LAN
/tool mac-server ping
set enabled=no
/tool netwatch
add disabled=yes down-script="/ip route disable [find comment=ISP1]" host=\
8.8.8.8 http-codes="" interval=10s test-script="" timeout=1s type=icmp \
up-script="/ip route enable [find comment=ISP1]"
add disabled=yes down-script="/ip route disable [find comment=LTE]" host=\
8.8.4.4 http-codes="" interval=10s test-script="" timeout=1s type=icmp \
up-script="/ip route enable [find comment=LTE]"