Everything stated seems reasonable except for this part… remember that I don’t want to set any IP settings on devices, everything should be done in router side.
Thats not how networking works, all the devices will get leased an IP address on their respective LAN. The access point also requires and IP address.
Now its clear that you really dont want TWO LANS, otherwise, why have each totally accessing each other. I can see that it may be an advantageous approach in terms of separating traffic for the internet as you desire. Finally perhaps there is some other reason for having two networks but I dont know that answer…
Start with a firewall approach that is basic and clean.
I made some adjustments for your scenario.
/ip firewall filter
{Input Chain}
add action=accept chain=input comment=“defconf: accept established,related,untracked” connection-state=established,related,untracked
add action=drop chain=input comment=“defconf: drop invalid” connection-state=invalid
add action=accept chain=input comment=“defconf: accept ICMP” protocol=icmp
add action=accept chain=input in-interface-list=LAN
add action=drop chain=input comment=“drop all else”
{forward chain}
add action=fasttrack-connection chain=forward comment=“defconf: fasttrack” connection-state=established,related
add action=accept chain=forward comment=“defconf: accept established,related, untracked” connection-state=established,related,untracked
add action=drop chain=forward comment=“defconf: drop invalid” connection-state=invalid
add action=accept chain=forward comment=“allow internet traffic” in-interface-list=LAN out-interface-list=WAN
add action=accept chain=forward comment=“allow port forwarding” connection-nat-state=dstnat
add action=accept chain=forward comment"allow intervlan traffic" in-interface-list=LAN out-interface-list=LAN
add action=drop chain=forward comment=“drop all else”
/ip firewall nat
either
add action=masquerade chain=srcnat comment=“defconf: masquerade” out-interface**-list=**WAN
OR
add action=masquerade chain=srcnat comment=“defconf: masquerade” out-interface=WANA1
add action=masquerade chain=srcnat comment=“defconf: masquerade” out-interface=WANB2
If your WANIPs provided by the modem/router are fixed private IPs then the format would be
/ip firewall nat
add action=srcnat chain=srcnat out-interface=WANA1 to-addresses=IP_WanA1
add action=srcnat chain=srcnat out-interface=WANB2 to-addresses=IP_WanB2
Note: Since at least one of the subnets should be capable of using both, there is no point in using source addresses for them.
Ensure the WAN interface includes members WANA1 and WANB2
Ensure the LAN interface includes members vlanAA and vlanBB
Create your two vlans for the subnets (will be easy to implement especially on the wifi side).
interface for vlans is bridge
vlans get ip pool, ip address, dhcp-server, dhcp-server network
Complete /interface bridge port setup (where you assign vlan to WLAN port (access port) for local wifi, assign vlan to local users via etherport (access port) and trunk port to smart devices.
Complete /interface bridge vlan setup
Turn bridge vlan filtering on.
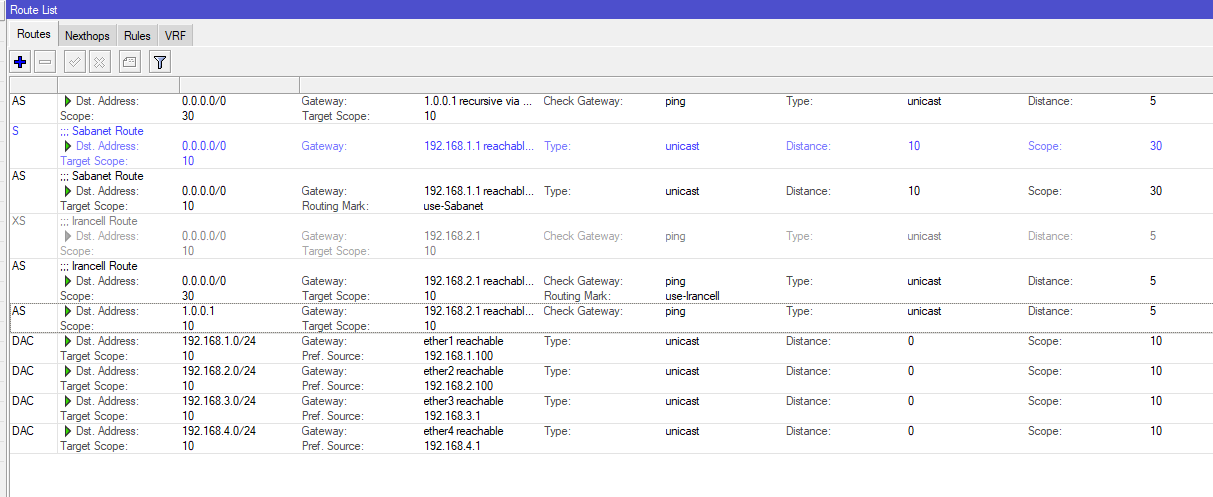
The real magic will be done on IP Routes.
Assuming you have public IPs then you dont even need IP DHCP client
Just assign the two WANIPs in the IP ADDRESS location in the config
add address=10.10.10.1/24 interface=ether1 network=10.10.10.0
add address=20.20.20.1/24 interface=ether2 network=20.20.20.0
/ip routes
dst-address=0.0.0.0/0 gwy=10.10.10.1 table=main distance=10
dst-address=0.0.0.0/0 gwy=20.20.20.1 table=main distance**=5** check-ping=gateway
This construct basically say ALL TRAFFIC will go to WanB because it has a shorter distance.
If Wan B is not available all traffic will be switched to WanA, but the router will keep checking to see if WanB comes backup on line and if does then all traffic will go there.
Thus we are partially there. We use simple failover to create the conditions for WANB that meet your requirements. Since all traffic goes to WANB, all WANB users go there.
If WANB fails, they will move to WANA. Check.
Now what about WANA users. We dont want them going to WANB, so we create a special FORCING route for them and thus require a third IP route.
ON version 7 firmware its something like
dst=address=0.0.0.0/0 gwy=10.10.10.1 table=useWAN-A
/routing table fib add name=useWAN-A
/routing rule add src-address=VLANAA/24 action=lookup-only-in-table table=useWAN-A
ON version 6 firmware its something like
dst-address=0.0.0.0/0 gwy=10.10.10.1 routing-mark=useWAN-A
/ip route rule
add action=lookup-only-in-table src-address=VLANAA/24 table=useWAN-A
Note: In both cases if you DID want VLANAA users to be able to access WAN B, if WANA goes down, then simply change action to LOOKUP (vice lookup-only-in table).
They will still be forced to use WANA all the time, unless its down.
++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
To clarify you will have two subnets on your router, is one of them trusted and not guests etc or IOT devices on it etc…
The trusted one should be the one that the admin resides on and where the admin will configure the devices from and all smart devices will get their IP from this subnet.
If both those vlans are not trusted, then consider a management vlan .