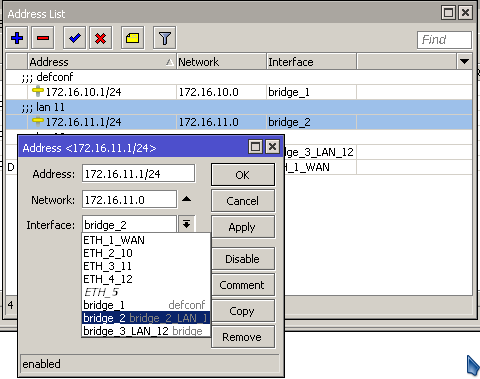
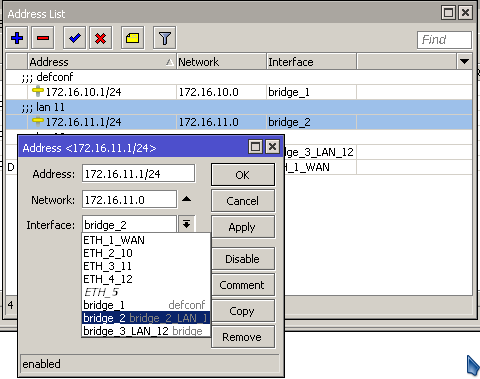
Having 2 LAN with different ports
172.16.10.x → Bridge 1
172.16.11.x → Bridge 2
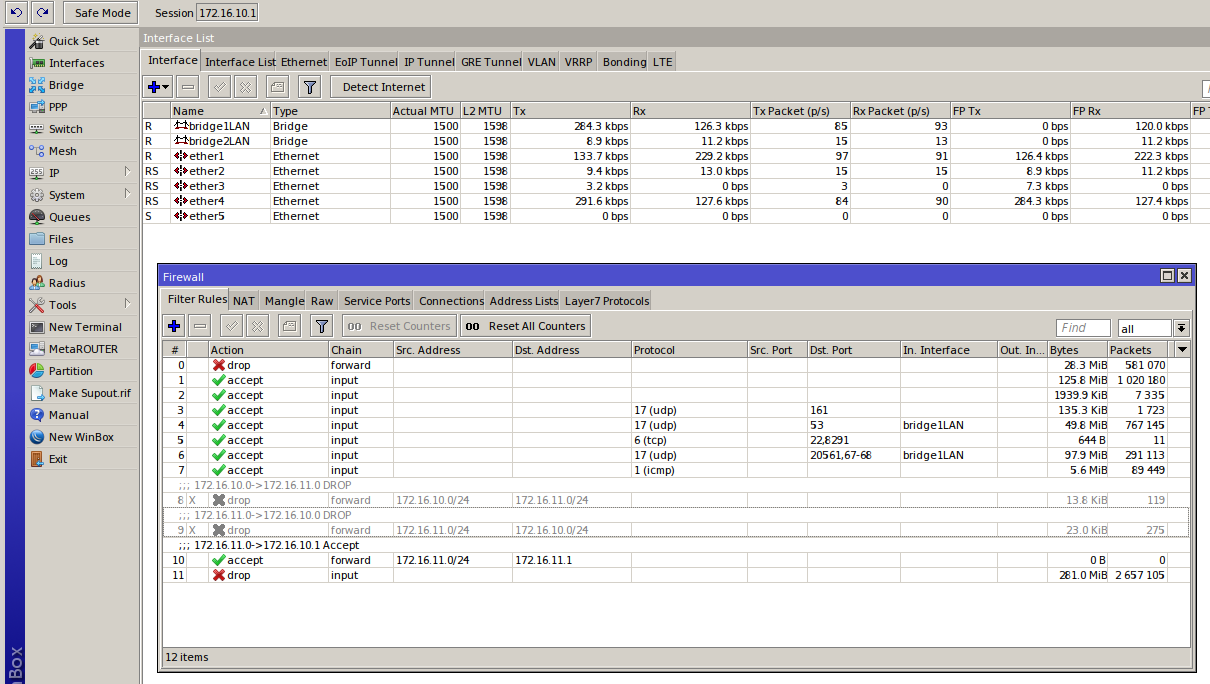
Having as rules into firewall (see attachment)
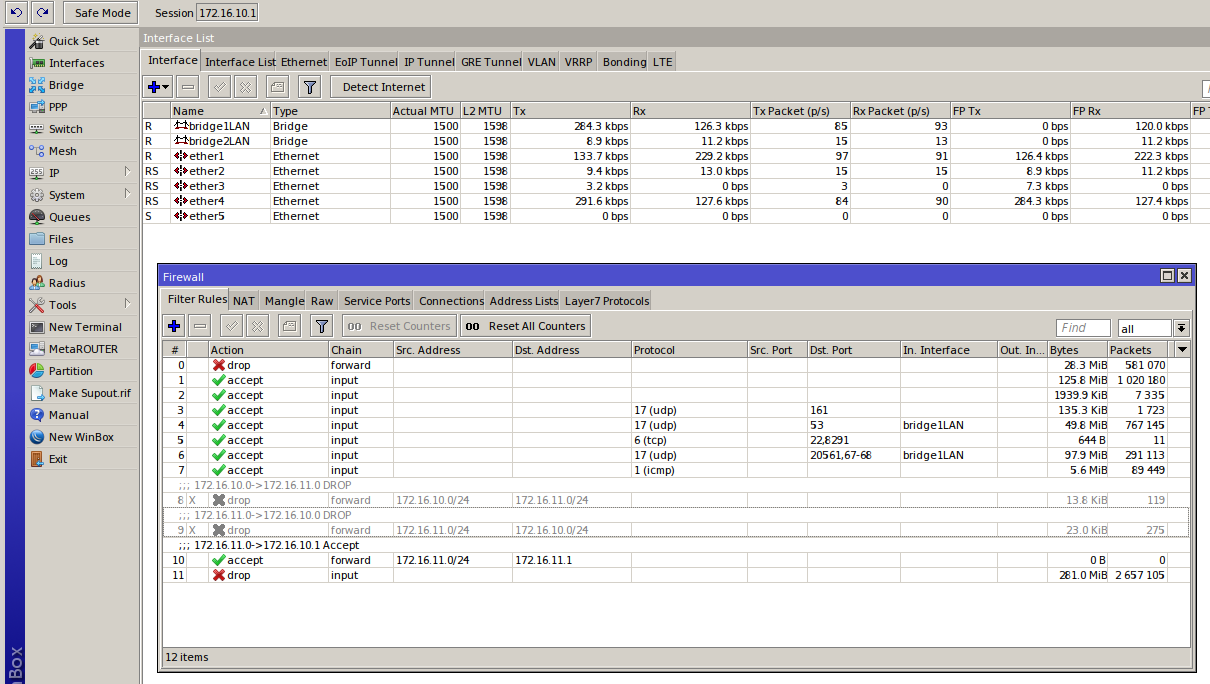
ip firewall filter add chain=forward src-address=172.16.10.0/24 dst-address=172.16.11.0/24 action=drop comment="172.16.10.0->172.16.11.0 DROP"
ip firewall filter add chain=forward src-address=172.16.11.0/24 dst-address=172.16.10.0/24 action=drop comment="172.16.11.0->172.16.10.0 DROP"
ip firewall filter add chain=forward src-address=172.16.11.0/24 dst-address=172.16.11.1 action=accept comment="172.16.11.0->172.16.10.1 Accept"
I’d like to allow connecting through ssh from 172.16.10.x => 172.16.11.x
Disabling the above rules I reach the goal but disabling any of the 2 first I can’t, How can I do that its possible to connect from a LAN to another but not the reverse?
Thx in advance
You will need to allow the return packets (from the LAN2 into LAN1) .
For this add on your drop rule connection state: “NEW” connections from LAN 2 into LAN 1, but accept “related”/established.
Thx for your kind answer, but as a newbie, and after having read your answer as many times as I could I’m unable to take it to concrete steps… could you help me more describing how precisely?
/ip firewall filter
add action=accept chain=forward dst-address=172.16.11.0/24 src-address=172.16.10.0/24
add action=accept chain=forward connection-state=established,related dst-address=172.16.10.0/24 src-address=172.16.11.0/24
add action=drop chain=forward connection-state=invalid,new dst-address=172.16.10.0/24 src-address=172.16.11.0/24
-Chris
Note that for that to be working which was not my case Both addresses in the lists have to be set to its corresponding bridges. By default the interfaces are talking to each other without restriction. You have to set rules to avoid the trafic from one subnet (172.16.10.x) to be able to talk to another (172.16.11.x) by adding a firewall rule to either reject (on LAN) or drop (for WAN) the traffic coming from the other interface.