This post has no real purpose.
I don't quite understand...
So let's say the RB has 192.168.7.1, and when a packet arrives on port 80 bound for 192.168.7.1,
it magically has to end up on port 80 of another IP, perhaps 10.2.3.4 used inside a container?
Do you know what this thing is called NAT?
Or did I misunderstand?
The container has to share the same IP address as the RouterBOARD?
Or are you saying that if the packet on port 80 is destined for container 10.2.3.4,
and for some mysterious reason,
RouterOS automatically changes the packet's destination IP to 192.168.7.1 just because it's destined for port 80?
This post has no real purpose.
This assumption is obviously wrong, because the containers have their own VETH interfaces, with their own IPv4 and IPv6 address assigned. The interfaces are not the one RouterOS uses for its services. The behavior you observed is solely a restriction of the softwares that you run inside your container or their configuration.
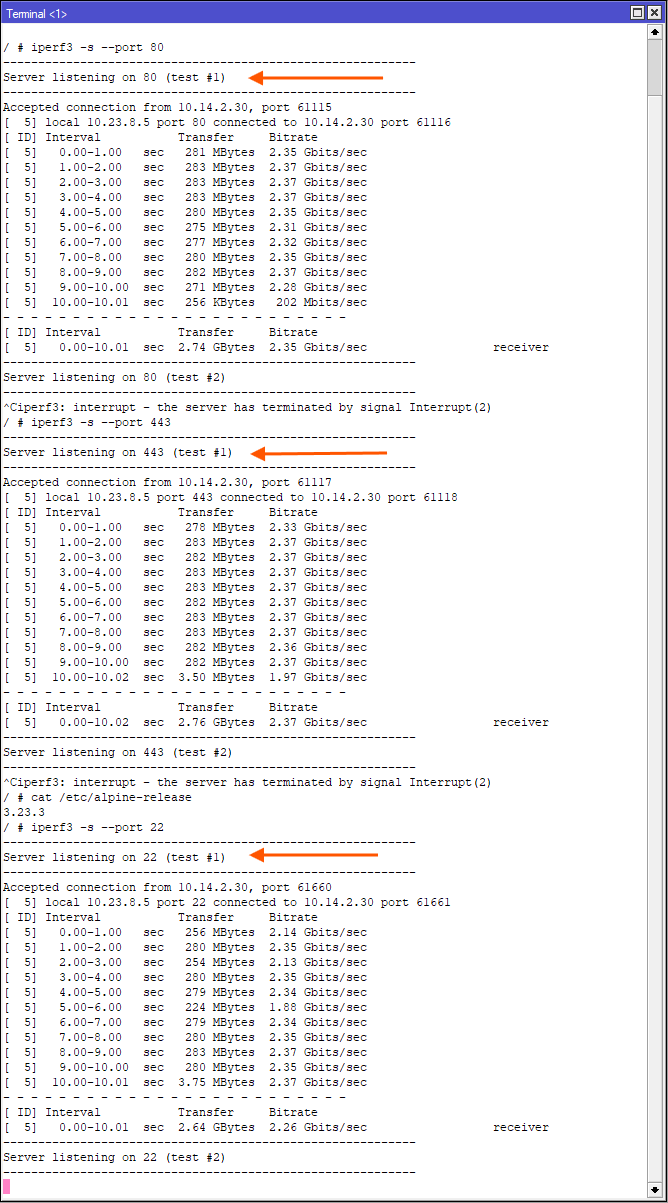
Case in point: I just fired up an Alpine (library/alpine:latest) container, added the iperf3 package with apk. And iperf3 running in server mode has no problem listening on all the ports you have in your screenshot, and can of course accept incoming connections:
Not sure I follow this either, I use dst nat for tcp port 443 to container ip and same port w/o issue (for WAN access), ROS www-ssl service is disabled in my case, but also ROS service port can be changed if service needs to be up and without conflicting with forwarded port.
For access over LAN or to different subnets with proper routing and firewall rules there is no need for NAT and same ports can be binded on ROS and container ip.
This post has no real purpose.
There's no need to belittle yourself, if is not sarcasm, just ask for specific requirements in detail and maybe someone will have specific answer.
For eg. in case where you have separate subnet for containers you can route traffic between subnets without need of dstnat from router IP. Also there is option to have container veth assingend to port of LAN bridge and use firewall filter rules to isolate container and allow trafic from LAN clients which are allowed to use it and drop traffic from container to LAN if is not needed. Etc…