There was a need to filter traffic/ban by MAC. I’ve figured out how to block MAC addresses in the Wi-Fi network using the Access List. And other options. However, I still haven’t managed to get MAC filtering working properly in the wired (bridge) network.
I understand that in theory I should use “/interface bridge filter” But I can’t figure out how to do it correctly. I keep getting an error.
Can you share the error message?
What kind of traffic do you want to filter? Bridge filters are primarily intended for LAN-to-LAN connections. You can use MAC address in IP firewall also.
Keep in mind, filtering by MAC address is fairly easy to bypass. Many smartphones, for example, don’t even require any special knowledge or tools to change device’s MAC address, just a few taps in configuration.
For example
/interface bridge filter add chain=forward in-bridge=bridge1 src-mac-address=AA:BB:CC:DD:EE:01 action=drop comment="MAC Ban"
expected / (line 1 column 95)
Not so much traffic, but other people’s PCs. Unfortunately, there is a possibility of connecting third-party devices. And not even just via Wi-Fi. I was thinking of creating a white list to be able to add my Mac to it.
Isn’t it easier then to use DHCP - static only ?
address-pool (string | static-only; Default: static-only) IP pool, from which to take IP addresses for the clients. If set to static-only, then only the clients that have a static lease (added in the lease submenu) will be allowed.
OK, so you want to block all access completely, understood. I was just checking if you wanted to block Internet access only, for example, while allowing LAN communication.
Your example will work if you add source MAC mask.
src-mac-address=AA:BB:CC:DD:EE:01/FF:FF:FF:FF:FF:FF
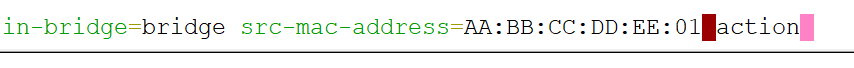
If you type your command as is in the terminal, you will see the syntax checker starts complaining right before the “action” keyword. Whenever you see this dark purple marker, you know something is wrong with the syntax.
Of course, you could also use WinBox where normally it will make things easier.
This is pretty much the only way to make MAC filtering work properly. Still, there are no guarantees since someone can spoof your MAC. If you want to take it to the next level, look into 802.1X.
It won’t prevent people from setting a static IP on their devices. But I agree, in a simple non-hostile environment this is the easiest way.
Yes, it works.
Whenever you see this dark purple marker, you know something is wrong with the syntax.
I understand that this is the first sign that there will be an error. I just didn’t know what it was called or how to explain it.
This is pretty much the only way to make MAC filtering work properly. Still, there are no guarantees since someone can spoof your MAC. If you want to take it to the next level, look into 802.1X.
I’m not very good at network settings, but I don’t quite understand what you’re talking about. If I bind Mac+IP, then this can also be bypassed.
I was referring to this: https://help.mikrotik.com/docs/spaces/ROS/pages/328090/Dot1X. It’s not a trivial thing, I’ve never used it myself. The idea is that nobody can get a device online without authentication, MACs or IPs don’t matter.
It all depends on your requirements—home use, business use etc. My guess is that MAC filtering will work fine for you.
MAC spoofing means if someone can guess (or sniff) the MAC address you whitelisted, then they can set their device to use this MAC and bypass your bridge filters.
It won’t prevent people from setting a static IP on their devices. But I agree, in a simple non-hostile environment this is the easiest way.
This needs to be combined with setting ARP mode to reply-only on the bridge/vlan interfaces, and then of course the parameter Add ARP For Leases also needs to be turned on for the DHCP Server instances (add-arp=yes).
I was referring to this: Dot1X - RouterOS - MikroTik Documentation. It’s not a trivial thing, I’ve never used it myself. The idea is that nobody can get a device online without authentication, MACs or IPs don’t matter.
Dot1X works very well in RouterOS (together with User Manager), I am using it right now. However, the client devices either have to be plugged directly to the MikroTik Routers/Switches, or if to 3rd party switches then they also have to support 802.1x. An alternative is to use Wireless APs with WPA2-Enterprise/WPA3-Enterprise support, which also implement 802.1x.