I have a failover working with netwatch rules and ive been trying to mess around with a way to break the connections tied to specific WANs so that when the failover happens
I can swiftly break all the connections only tied to the WAN that failed
I’ll add my forward chain rules.. routes.. mangle and netwatch rules.
I was wondering if doing this in any way breaks fast track before im using Mangle (even tho that particular network, I have rules above that are capturing those packets before fast track, but just kind want to know.)
And while testing, I do notice that fail over works, but connecting to the same site that I was connected to before does take a bit to re-establish, ive confirmed in connection tracking that the connections are actually cleared too.
Thank you !
Forward Chain
[joshhboss@CCR2116] /ip/firewall/filter> print where chain=forward
Flags: X - disabled, I - invalid; D - dynamic
0 D ;;; special dummy rule to show fasttrack counters
chain=forward action=passthrough
1 ;;; SimpleQueue Established,Related, SRC
chain=forward action=accept connection-state=established,related src-address-list=SimpleQueueList log=no log-prefix=""
2 ;;; SimpleQueue Established,Related, DST
chain=forward action=accept connection-state=established,related dst-address-list=SimpleQueueList log=no log-prefix=""
3 ;;; defconf: fasttrack
chain=forward action=fasttrack-connection hw-offload=yes connection-state=established,related connection-mark=no-mark log=no log-prefix=""
4 ;;; defconf: accept established,related, untracked
chain=forward action=accept connection-state=established,related,untracked
5 ;;; defconf: drop invalid
chain=forward action=drop connection-state=invalid
6 ;;; Allow-AP-TO-Controllers
chain=forward action=accept src-address-list=10AP-Management dst-address-list=AllowRemoteControllers log=no log-prefix=""
7 ;;; AllowInternet For LAN
chain=forward action=accept in-interface-list=EV-LAN out-interface-list=WAN log=no log-prefix=""
8 ;;; Allow Authorized ALL
chain=forward action=accept src-address-list=Authorized log=no log-prefix=""
9 X ;;; AllPortForwarding
chain=forward action=accept connection-state="" connection-nat-state=dstnat in-interface-list=WAN log=no log-prefix=""
10 ;;; DROP ALL ELSE
chain=forward action=drop log=no log-prefix=""
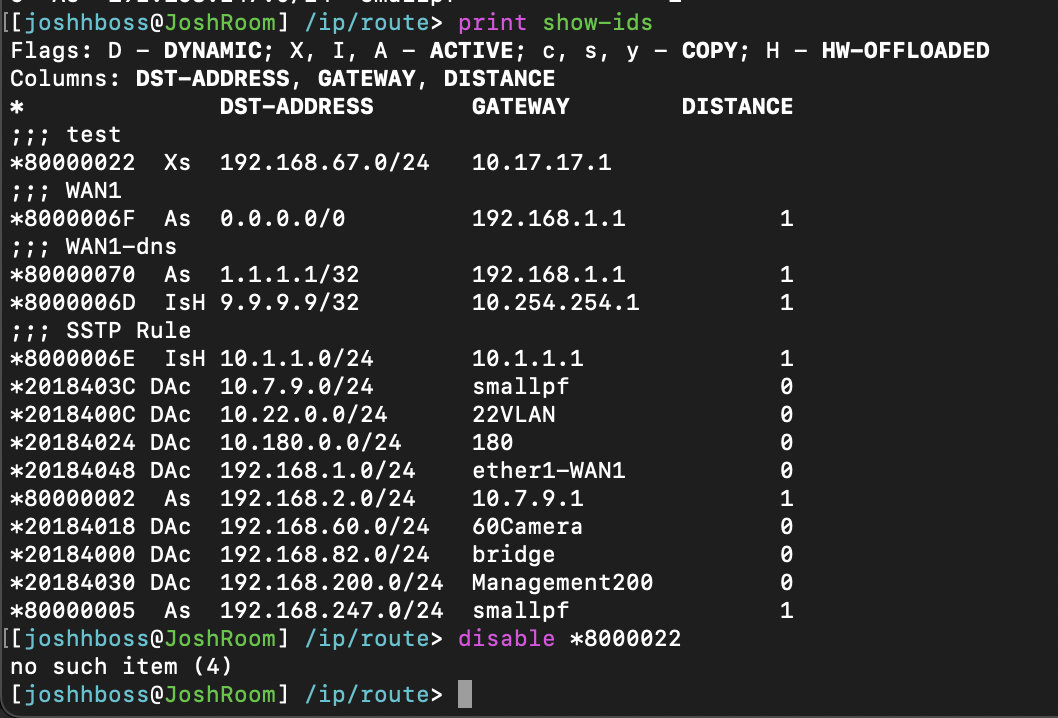
Routes
[joshhboss@CCR2116] /ip/route> print where dynamic=no
Flags: A - ACTIVE; s - STATIC
Columns: DST-ADDRESS, GATEWAY, DISTANCE
# DST-ADDRESS GATEWAY DISTANCE
;;; WAN2
0 s 0.0.0.0/0 192.168.95.1 2
;;; WAN1
1 As 0.0.0.0/0 192.168.2.1 1
;;; WAN2-dns
2 As 1.0.0.1/32 192.168.95.1 1
;;; WAN1-dns
3 As 1.1.1.1/32 192.168.2.1 1
;;; WAN1-21
4 As 0.0.0.0/0 192.168.95.1 1
;;; WAN2-21
5 s 0.0.0.0/0 192.168.2.1 2
Mangle
[joshhboss@CCR2116] /ip/firewall/mangle> print where dynamic=no
Flags: X - disabled, I - invalid; D - dynamic
3 chain=prerouting action=mark-connection new-connection-mark=useWAN2 passthrough=yes connection-state=new in-interface=250Vlan log=no log-prefix=""
Netwatch
add comment="Internet Test - WAN2" disabled=no down-script=\
"/ip route disable [find where comment=WAN1-21]\r\
\n/ip firewall connection\r\
\n:foreach idc in=[find where (timeout>60) || (connection-mark=useWAN2)] do={\r\
\n remove [find where .id=\$idc]\r\
\n}\r\
\n" host=1.0.0.1 http-codes="" test-script="" thr-avg=700ms thr-jitter=2s thr-max=2s thr-stdev=500ms type=icmp up-script=\
"/ip route enable [find where comment=WAN1-21]\r\
\n/ip firewall connection\r\
\n:foreach idc in=[find where (timeout>60) || (connection-mark=useWAN2)] do={\r\
\n remove [find where .id=\$idc]\r\
\n}\r\
\n"
I did originally try and just have
/ip route enable [find where comment=WAN1-21]
/ip firewall connection remove [find where connection-mark=useWAN2]