Folks,
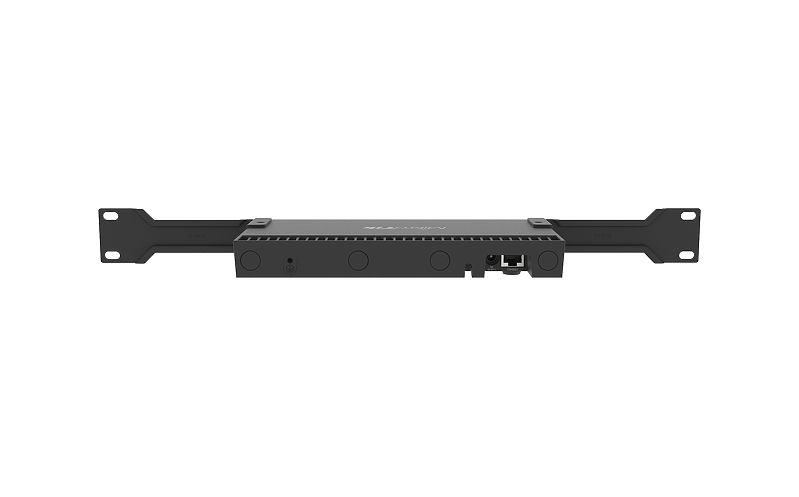
I am new to Mikrotik and getting a little frustrated with the documentation and the over abundance of options and lack of clarity in some of the documentation. The bridge concept (bridge VLAN fltering) I figured out after pounding my head and realizing that the RB4011 has low-level realtek switch chips and hence no HW offload. So I got past all of that documentation sending me sideways. So I am stuck getting proper management VLAN access to winbox from my router : RB4011 (RouterOS 6.47.7) internally to the devices or downstream from the new switch css326-24G (Swos 2.12)
I have my VLANs setup and working properly for production nets, left is access to setting up the "recommended" bridges and switching for management VLANS where I want to accomplish seemingly easy config but I can only get access to the router through a port which has by default VLAN 1 untagged on it.
Here is what I am trying to accomplish:
Setup a management VLAN across both devices, on workstation on an access port in the switch, another on the RB4011 for "emergency" and a third port for non-bridge "911 emergencies".
Current Config:
By default the IP of the RB4011 is 72.1 and the switch 72.2. The default address table has it in there and running in a switch port (not the bridge)
I have the management LAN (1372 - Dot 13) on the router on ether 9 (untagged), the bridge, SFP (tagged). On the downstream switch I have a hybrid port setup (untagged vlan10, tagged 1372) and have VLAN tagging setup on the workstation and the untagged VLAN. Untagged works fine, tagged no.
Neither the ether 9 nor the tagged workstation can get access to the router (.1) but can to the switch (.2) I can ping .1 but remon/connect no go.
I put Port 10 (ether10) to VLAN 1 untagged and this is the only way I can get access to winbox.
Question1: Is this following the best practices, and if not what is preferred.
Question 2:: What am I doing wrong here? I am a bit confused on access to router service when overlaying bridge/VLAN for management. I would like to not use VLAN 1 for anything.
Question 3: I would like to make ether 8 the "911 emergency" port, so I took it out of the bridge and left it in a switch group. However no matter what I do I cannot access this port, and it doesnt connect to anything. I noticed the default fw rules refer to LAN as an interface-group of the bridge, and that may be an issue but I am a noob here with mikrotik.
Thanks
VLAN table:
BRIDGE VLAN-IDS CURRENT-TAGGED CURRENT-UNTAGGED
0 Br_VLAN 10 Br_VLAN
SFP_Switch
1 Br_VLAN 50 Br_VLAN P2_Obihai
SFP_Switch P5_Inverter
P3_Alarm
2 Br_VLAN 1372 Br_VLAN
SFP_Switch
3 Br_Emerg 1
4 D Br_VLAN 1 Br_VLAN
SFP_Switch
P10_BridgeAccess
Networks: (redacted WAN, working)
ADDRESS NETWORK INTERFACE
0 ;;; defconf
192.168.72.1/24 192.168.72.0 P2_Obihai
1 192.168.50.1/24 192.168.50.0 VLAN_50
2 192.168.10.1/24 192.168.10.0 VLAN_10
3 192.168.13.1/24 192.168.13.0 VLAN_MGMT
Firewall (I kept it basic for now)
0 D ;;; special dummy rule to show fasttrack counters
chain=forward action=passthrough
1 ;;; defconf: accept established,related,untracked
chain=input action=accept connection-state=established,related,untracked
2 ;;; defconf: drop invalid
chain=input action=drop connection-state=invalid
3 ;;; defconf: accept ICMP
chain=input action=accept protocol=icmp
4 ;;; defconf: accept to local loopback (for CAPsMAN)
chain=input action=accept dst-address=127.0.0.1
5 ;;; defconf: drop all not coming from LAN
chain=input action=drop in-interface-list=!LAN
6 ;;; defconf: fasttrack
chain=forward action=fasttrack-connection connection-state=established,related
7 ;;; defconf: accept established,related, untracked
chain=forward action=accept connection-state=established,related,untracked
8 ;;; defconf: accept in ipsec policy
chain=forward action=accept ipsec-policy=in,ipsec
9 ;;; defconf: accept out ipsec policy
chain=forward action=accept ipsec-policy=out,ipsec
10 ;;; defconf: drop invalid
chain=forward action=drop connection-state=invalid
11 ;;; defconf: drop all from WAN not DSTNATed
chain=forward action=drop connection-state=new connection-nat-state=!dstnat in-interface-list=WAN