Hello everyone,
Could you please help me with a routing issue I’ve got with my site-to-site VPN setup?
Problem: Mikrotik hAP ax² fails to forward response packets back via VPN tunnel. Packets are being dropped by firewall as “invalid”.
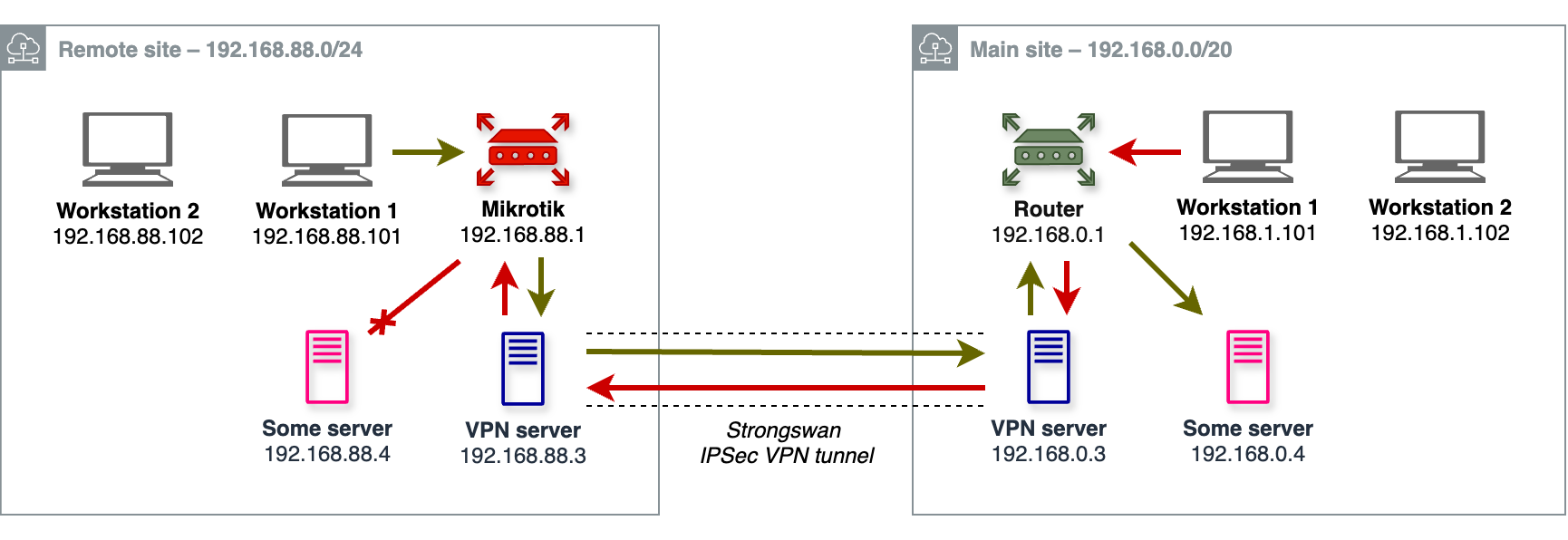
Main site (pictured on the right) unites several VLANS: 192.168.0.0/24, 192.168.1.0/24, etc. A 3rd party router is configured to route requests to 192.168.88.0/24 network via a VPN server at 192.168.0.3. The VPN server is running Strongswan and is properly configured to route 192.168.88.0/24 to a remote VPN server and 192.168.0.0/20 to the local router.
Remote site (pictured on the left) includes a single 192.168.88.0/24 LAN, a Strongswan VPN server at 192.168.88.3 configured to route 192.168.0.0/20 through the tunnel, and a Mikrotik router at 192.168.88.1, with a static route:
;;; Main Site access via Strongswan IPSec tunnel
dst-address=192.168.0.0/20 routing-table=main pref-src="" gateway=192.168.88.3
immediate-gw=192.168.88.3%bridge distance=1 scope=30 target-scope=10 suppress-hw-offload=no
Remote site hosts can seamlessly access the entire Main site network. For instance, 192.168.88.101 workstation reaches 192.168.0.4 server through the tunnel with no issues (see green arrows).
Main site hosts, however, can only access remote VPN server (see red arrows) and Mikrotik router itself (can ping, ssh, http, etc. 192.168.88.1 and 192.168.88.3), but nothing else on the Remote site. I can’t ping 192.168.88.4 neither from 192.168.1.101 workstation nor from 192.168.0.3 VPN server.
After looking closely at the issue, I’ve found out that when a connection is being initiated from the Main site, packets that should be returned back to the Main site are being dropped on the Mikrotik by this firewall rule:
;;; defconf: drop invalid
chain=forward action=drop connection-state=invalid log=no log-prefix=""
With logging on, I see the following after running “ping 192.168.88.4” or “curl 192.168.88.4” on 192.168.1.101:
forward: in:bridge out:bridge, connection-state:invalid src-mac 5c:e9:1e:8d:39:41, proto ICMP (type 0, code 0), 192.168.88.4->192.168.1.101, len 84
forward: in:bridge out:bridge, connection-state:invalid src-mac 5c:e9:1e:8d:39:41, proto TCP (SYN,ACK), 192.168.88.4:80->192.168.1.101:36656, len 64
With the “forward chain → drop invalid” firewall rule disabled everything works both ways!
What am I missing? Why my static route does not help Mikrotik to route packets back to the Main site? Why are they considered “invalid”?
I would greatly appreciate any ideas. Thanks!