Hi everyone,
just bought my first MikroTik hEX. I'm struggling with something which to me should be straightforward.
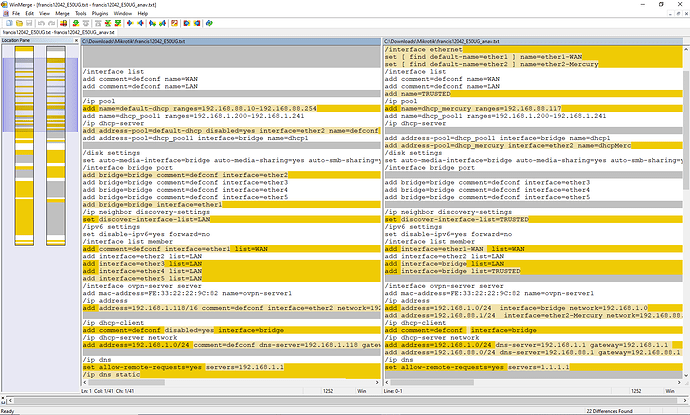
Below i'll attach my current config.
My setup is this
Internet --- ISP router (LAN port) ---- (internet port) hEX (LAN port) ---- (WAN port) Mercusys router (192.168.1.117)
Mercusys clients have a subnet of their own 192.168.8.0/24, while the main network is 192.168.1.0/24
I want the hEX to drop traffic coming from 192.168.8.0/24 and directed to 192.168.1.0/24 (ISP router excluded, so still allowing internet access).
I’ve set up a firewall rule but seems uneffective. I think that maybe the mercusys addresses may not appear to the hEX due to natting or something, but at least the traffic from the mercusys router should be caught…
Thank you,
any help or suggestions are welcome
# 2025-11-05 20:21:26 by RouterOS 7.20.2
# software id = DZG0-KHZX
#
# model = E50UG
# serial number = byebye
/interface bridge
add admin-mac=F4:1E:57:7E:7E:91 auto-mac=no comment=defconf name=bridge
/interface list
add comment=defconf name=WAN
add comment=defconf name=LAN
/ip pool
add name=default-dhcp ranges=192.168.88.10-192.168.88.254
add name=dhcp_pool1 ranges=192.168.1.200-192.168.1.241
/ip dhcp-server
add address-pool=default-dhcp disabled=yes interface=ether2 name=defconf
add address-pool=dhcp_pool1 interface=bridge name=dhcp1
/disk settings
set auto-media-interface=bridge auto-media-sharing=yes auto-smb-sharing=yes
/interface bridge port
add bridge=bridge comment=defconf interface=ether2
add bridge=bridge comment=defconf interface=ether3
add bridge=bridge comment=defconf interface=ether4
add bridge=bridge comment=defconf interface=ether5
add bridge=bridge interface=ether1
/ip neighbor discovery-settings
set discover-interface-list=LAN
/ipv6 settings
set disable-ipv6=yes forward=no
/interface list member
add comment=defconf interface=ether1 list=WAN
add interface=ether2 list=LAN
add interface=ether3 list=LAN
add interface=ether4 list=LAN
add interface=ether5 list=LAN
/interface ovpn-server server
add mac-address=FE:33:22:22:9C:82 name=ovpn-server1
/ip address
add address=192.168.1.118/16 comment=defconf interface=ether2 network=192.168.0.0
/ip dhcp-client
add comment=defconf disabled=yes interface=bridge
/ip dhcp-server network
add address=192.168.1.0/24 comment=defconf dns-server=192.168.1.118 gateway=192.168.1.118 netmask=24
/ip dns
set allow-remote-requests=yes servers=192.168.1.1
/ip dns static
add address=192.168.1.118 comment=defconf name=router.lan type=A
/ip firewall address-list
add address=192.168.1.2-192.168.1.255 comment="Vodafone Station Lan / senza Router" list=VF_Lan
add address=192.168.8.0/24 comment="Mercusys LAN" list=Mercusys_LAN
/ip firewall filter
add action=drop chain=forward comment="DROP Mercusys to Vodafone LAN" dst-address-list=VF_Lan in-interface-list=all out-interface-list=all src-address=192.168.1.117 src-address-list=Mercusys_LAN
add action=accept chain=input comment="Accept Management from TUF" disabled=yes dst-address=192.168.1.118 dst-port=8291 protocol=tcp src-address=192.168.1.28
add action=accept chain=input comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=invalid
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment="defconf: accept to local loopback (for CAPsMAN)" dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" connection-state=established,related hw-offload=yes
add action=accept chain=forward comment="defconf: accept established,related, untracked" connection-state=established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid / Questa rompe spesso navigazione" connection-state=invalid disabled=yes
add action=drop chain=forward comment="defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat connection-state=new in-interface-list=WAN
/ip firewall nat
add action=masquerade chain=srcnat comment="defconf: masquerade" ipsec-policy=out,none out-interface-list=WAN
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only " list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
/ipv6 firewall filter
add action=accept chain=input comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" dst-port=33434-33534 protocol=udp
add action=accept chain=input comment="defconf: accept DHCPv6-Client prefix delegation." dst-port=546 protocol=udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=ipsec-esp
add action=accept chain=input comment="defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment="defconf: drop everything else not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" connection-state=invalid
add action=drop chain=forward comment="defconf: drop packets with bad src ipv6" src-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: drop packets with bad dst ipv6" dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=500,4500 protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=ipsec-esp
add action=accept chain=forward comment="defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment="defconf: drop everything else not coming from LAN" in-interface-list=!LAN
/system clock
set time-zone-name=Europe/Rome
/tool mac-server
set allowed-interface-list=LAN
/tool mac-server mac-winbox
set allowed-interface-list=LAN