I am not sure how you are pasting your configs, but it appears like you are pasting and then formatting after the format has already been "tainted".
If you press the </> icon in the ribbon, then paste the output from a winbox terminal directly into the forum, it should look more like the following:
# 2025-12-01 01:07:41 by RouterOS 7.21beta11
# software id = 9NNQ-BRU3
#
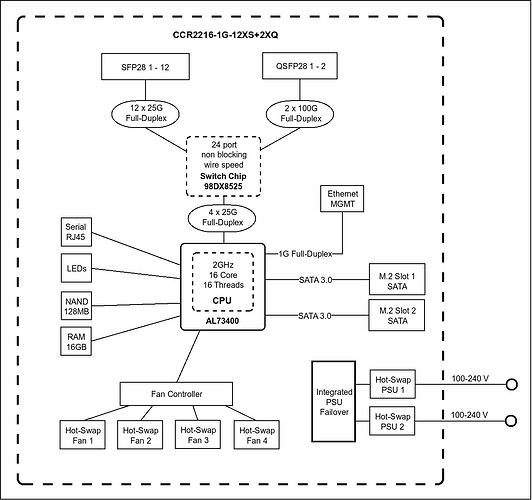
# model = CCR2216-1G-12XS-2XQ
# serial number =
/interface bridge
add igmp-snooping=yes name=bridge1 vlan-filtering=yes
/interface ethernet
set [ find default-name=qsfp28-1-3 ] advertise="10M-baseT-half,10M-baseT-full,100M-baseT-half,100M-baseT-full,1G-baseT-half,1G-baseT-full,1G-baseX,2.5G-baseT,2.5G-baseX,5G-baseT,10G-baseT,10G-baseSR-LR,10G-baseCR,40G-baseSR4-LR4,40G-bas\
eCR4,25G-baseSR-LR,25G-baseCR,50G-baseSR2-LR2,50G-baseCR2"
set [ find default-name=qsfp28-2-3 ] advertise="10M-baseT-half,10M-baseT-full,100M-baseT-half,100M-baseT-full,1G-baseT-half,1G-baseT-full,1G-baseX,2.5G-baseT,2.5G-baseX,5G-baseT,10G-baseT,10G-baseSR-LR,10G-baseCR,40G-baseSR4-LR4,40G-bas\
eCR4,25G-baseSR-LR,25G-baseCR,50G-baseSR2-LR2,50G-baseCR2"
set [ find default-name=sfp28-1 ] fec-mode=fec91
set [ find default-name=sfp28-2 ] auto-negotiation=no speed=10G-baseCR
/interface vlan
add interface=bridge1 l3-hw-offloading=no name=vlan10 vlan-id=10
/interface list
add name=WAN
add name=LAN
/ip pool
add name=dhcp_pool1 ranges=10.0.0.100-10.0.0.254
add name=dhcp_pool10 ranges=10.0.10.100-10.0.10.254
/ip dhcp-server
add address-pool=dhcp_pool1 interface=bridge1 name=dhcp1
add address-pool=dhcp_pool10 interface=vlan10 name=dhcp10
/interface bridge port
add bridge=bridge1 interface=qsfp28-1-1
add bridge=bridge1 interface=qsfp28-1-2
add bridge=bridge1 interface=qsfp28-1-3
add bridge=bridge1 interface=qsfp28-1-4
add bridge=bridge1 interface=qsfp28-2-1
add bridge=bridge1 interface=qsfp28-2-2
add bridge=bridge1 interface=qsfp28-2-3
add bridge=bridge1 interface=qsfp28-2-4
add bridge=bridge1 interface=sfp28-2
add bridge=bridge1 interface=sfp28-3
add bridge=bridge1 interface=sfp28-4
add bridge=bridge1 interface=sfp28-5
add bridge=bridge1 interface=sfp28-6
add bridge=bridge1 interface=sfp28-7
add bridge=bridge1 interface=sfp28-8
add bridge=bridge1 interface=sfp28-9
add bridge=bridge1 interface=sfp28-10
add bridge=bridge1 interface=sfp28-11
add bridge=bridge1 interface=sfp28-12
/ipv6 settings
set accept-router-advertisements=yes
/interface bridge vlan
add bridge=bridge1 tagged=sfp28-6 vlan-ids=10
/interface list member
add interface=sfp28-1 list=WAN
add interface=bridge1 list=LAN
/ip address
add address=10.0.0.1/24 interface=bridge1 network=10.0.0.0
add address=192.168.77.1/30 comment=management interface=ether1 network=192.168.77.0
add address=10.0.10.1/24 interface=vlan10 network=10.0.10.0
/ip cloud
set update-time=no
/ip dhcp-client
add interface=sfp28-1
/ip dhcp-server network
add address=10.0.0.0/24 dns-server=10.0.0.1 gateway=10.0.0.1
add address=10.0.10.0/24 dns-server=10.0.10.1 gateway=10.0.10.1
/ip dns
set allow-remote-requests=yes verify-doh-cert=yes
/ip firewall filter
add action=accept chain=input comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=invalid
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment="defconf: accept to local loopback (for CAPsMAN)" dst-address=127.0.0.1
add action=accept chain=input comment="allow igmpv2" protocol=igmp
add action=accept chain=input comment="allow new TV7 MCast streams" dst-address=233.50.230.0/24 dst-port=5000 protocol=udp src-address=77.109.129.0/24
add action=drop chain=input comment="defconf: drop all not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment="defconf: accept in ipsec policy" ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" connection-state=established,related
add action=accept chain=forward comment="defconf: accept established,related, untracked" connection-state=established,related,untracked
add action=accept chain=forward comment="allow forwarding of IPTV TV7" dst-address=233.50.230.0/24 dst-port=5000 protocol=udp
add action=drop chain=forward comment="defconf: drop invalid" connection-state=invalid
add action=drop chain=forward comment="defconf: drop all from WAN not DSTNATed" connection-nat-state=!dstnat connection-state=new in-interface-list=WAN
/ip firewall nat
add action=masquerade chain=srcnat ipsec-policy=out,none out-interface-list=WAN
/ip service
set ftp disabled=yes
set telnet disabled=yes
set www disabled=yes
set www-ssl certificate=webfig disabled=no
/ip ssh
set strong-crypto=yes
/ipv6 address
add address=::401:0:0:0:1 from-pool=v6pool interface=bridge1
add address=::400:0:0:0:1 from-pool=v6pool interface=vlan10
/ipv6 dhcp-client
add add-default-route=yes default-route-tables=main interface=sfp28-1 pool-name=v6pool request=address,prefix
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only" list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
/ipv6 firewall filter
add action=accept chain=input comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" dst-port=33434-33534 protocol=udp
add action=accept chain=input comment="defconf: accept DHCPv6-Client prefix delegation" dst-port=546 protocol=udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=ipsec-esp
add action=accept chain=input comment="defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment="defconf: drop everything else not coming from LAN" in-interface-list=!LAN
add action=fasttrack-connection chain=forward comment="defconf: fasttrack6" connection-state=established,related
add action=accept chain=forward comment="defconf: accept established,related,untracked" connection-state=established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" connection-state=invalid
add action=drop chain=forward comment="defconf: drop packets with bad src ipv6" src-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: drop packets with bad dst ipv6" dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=500,4500 protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=ipsec-esp
add action=accept chain=forward comment="defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment="defconf: drop everything else not coming from LAN" in-interface-list=!LAN
/ipv6 nd
set [ find default=yes ] advertise-dns=yes disabled=yes
add advertise-dns=yes interface=bridge1
add advertise-dns=yes interface=vlan10
/routing igmp-proxy
set quick-leave=yes
/routing igmp-proxy interface
add alternative-subnets=77.109.129.0/24 interface=sfp28-1 upstream=yes
add interface=bridge1
/system clock
set time-zone-autodetect=no time-zone-name=Europe/Zurich
/system ntp client
set enabled=yes
/system ntp client servers
add address=ntp.metas.ch
/system package update
set channel=testing
/system routerboard settings
set enter-setup-on=delete-key
/tool bandwidth-server
set enabled=no
/tool mac-server
set allowed-interface-list=none
/tool mac-server mac-winbox
set allowed-interface-list=none
/tool mac-server ping
set enabled=no
I ran your text through awk 'NF' to remove the blank lines.