Hello!
For the past few days I have been trying to set up my new router (hAP ax3) for my home. I don’t need anything to complicated for now. Just a handful of clients and a few resources I want to access securely from remote. Now I have been trying out the Back-To-Home feature and this works like a charm.
I wanted to try to set it up by myself as I wasn’t satisfied with the speed. I think the slow connection of the BTH VPN is cause by going trough Mikrotiks relay server. This assumption is based on that in the BTH config window the following message is dispayed at the bottom: “Router is behind NAT. Remote connection might not work”. As mentioned this does work - even for multiple clients at once. I am really struggling with setting up Wireguard by myself as I just can’t understand why I am not able to reach my LAN.
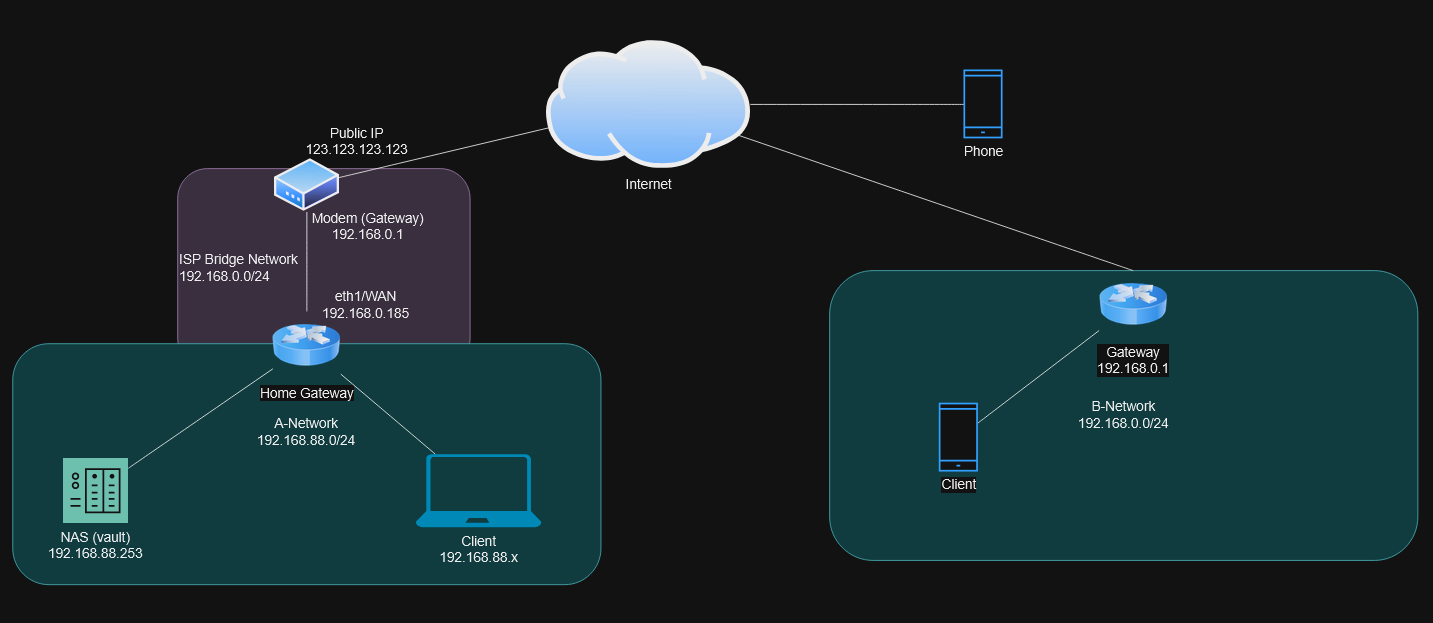
The following represents the topology:
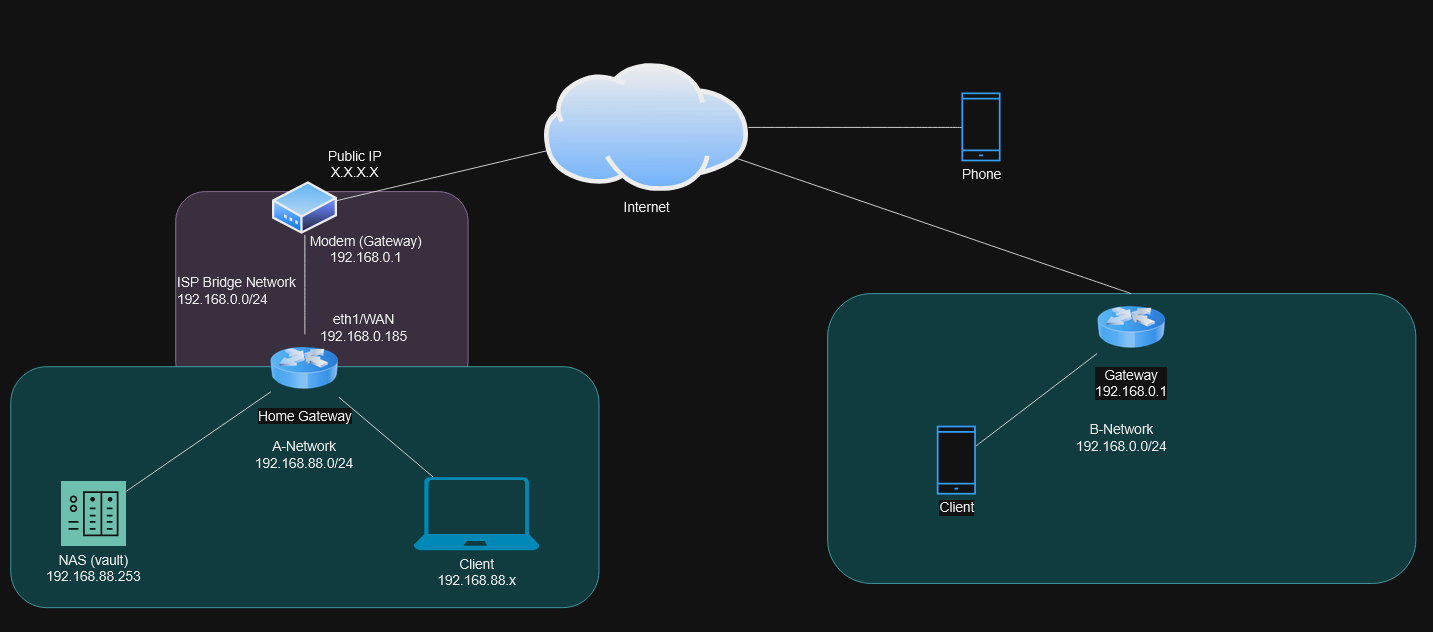
My ISP has the requirement to use their modem but it is possible to switch it over to a bridge mode which in essence relays everything to my Home Gateway - so my Home Gateway is setup as a DHCP client on the WAN side (eth1).
I would like to be able to access the A-Network(Home) from B with Wireguard server running on my Home Gateway and furthermore I would like to be able to access the resources at Home from my mobile phone.
I don’t know what I am doing wrong here and what I am missing?
The config of my Home Gateway:
/interface bridge
add admin-mac=78:9A:18:8C:1A:AC auto-mac=no comment=defconf name=bridge \
port-cost-mode=short
/interface wifi
set [ find default-name=wifi1 ] channel.band=5ghz-ax .skip-dfs-channels=\
10min-cac .width=20/40/80mhz configuration.mode=ap .ssid=MySSID-5GHz \
disabled=no security.authentication-types=wpa2-psk,wpa3-psk
set [ find default-name=wifi2 ] channel.band=2ghz-ax .skip-dfs-channels=\
10min-cac .width=20/40mhz configuration.mode=ap .ssid=MySSID disabled=no \
security.authentication-types=wpa2-psk,wpa3-psk
/interface wireguard
add comment=back-to-home-vpn listen-port=3496 mtu=1420 name=back-to-home-vpn
add comment=wireguard1 listen-port=13231 mtu=1420 name=wireguard1
/interface list
add comment=defconf name=WAN
add comment=defconf name=LAN
/ip pool
add name=default-dhcp ranges=192.168.88.10-192.168.88.254
/ip dhcp-server
add address-pool=default-dhcp interface=bridge lease-time=10m name=defconf
/interface bridge port
add bridge=bridge comment=defconf interface=ether2 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether3 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether4 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=ether5 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=wifi1 internal-path-cost=10 \
path-cost=10
add bridge=bridge comment=defconf interface=wifi2 internal-path-cost=10 \
path-cost=10
/ip neighbor discovery-settings
set discover-interface-list=LAN
/interface list member
add comment=defconf interface=bridge list=LAN
add comment=defconf interface=ether1 list=WAN
add comment=wireguard1 interface=wireguard1 list=LAN
/interface wireguard peers
add allowed-address=192.168.216.3/32 comment=\
"back-to-home-vpn | Phone" interface=back-to-home-vpn \
persistent-keepalive=5s public-key=\
"PK"
add allowed-address=192.168.100.2/32 comment="wireguard1 | Phone" \
interface=wireguard1 public-key=\
"PK"
/ip address
add address=192.168.88.1/24 comment=defconf interface=bridge network=\
192.168.88.0
add address=192.168.100.1/24 comment=wireguard1 interface=wireguard1 network=\
192.168.100.0
/ip cloud
set back-to-home-vpn=enabled ddns-enabled=yes
/ip dhcp-client
add comment=defconf interface=ether1
/ip dhcp-server network
add address=192.168.88.0/24 comment=defconf dns-server=192.168.88.1 gateway=\
192.168.88.1
/ip dns
set allow-remote-requests=yes
/ip dns static
add address=192.168.88.1 comment=defconf name=router.lan
/ip firewall filter
add action=accept chain=input comment=wireguard1 dst-port=13231 log=yes \
log-prefix="[WG1]" protocol=udp
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid log=yes log-prefix="[DROP-5]"
add action=accept chain=input comment="defconf: accept ICMP" protocol=icmp
add action=accept chain=input comment=\
"defconf: accept to local loopback (for CAPsMAN)" dst-address=127.0.0.1
add action=drop chain=input comment="defconf: drop all not coming from LAN" \
in-interface-list=!LAN log=yes log-prefix="[DROP-8]"
add action=accept chain=forward comment="defconf: accept in ipsec policy" \
ipsec-policy=in,ipsec
add action=accept chain=forward comment="defconf: accept out ipsec policy" \
ipsec-policy=out,ipsec
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related hw-offload=yes
add action=accept chain=forward comment=\
"defconf: accept established,related, untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" connection-state=\
invalid log=yes log-prefix="[DROP-13]"
add action=drop chain=forward comment="defconf: drop all from WAN not DSTNATed" \
connection-nat-state=!dstnat connection-state=new in-interface-list=WAN \
log=yes log-prefix="[DROP-14]"
/ip firewall nat
add action=masquerade chain=srcnat comment=wireguard1 log=yes log-prefix=\
"[WG1]" src-address=192.168.100.0/24
add action=masquerade chain=srcnat comment="defconf: masquerade" ipsec-policy=\
out,none out-interface-list=WAN
/ipv6 firewall address-list
add address=::/128 comment="defconf: unspecified address" list=bad_ipv6
add address=::1/128 comment="defconf: lo" list=bad_ipv6
add address=fec0::/10 comment="defconf: site-local" list=bad_ipv6
add address=::ffff:0.0.0.0/96 comment="defconf: ipv4-mapped" list=bad_ipv6
add address=::/96 comment="defconf: ipv4 compat" list=bad_ipv6
add address=100::/64 comment="defconf: discard only " list=bad_ipv6
add address=2001:db8::/32 comment="defconf: documentation" list=bad_ipv6
add address=2001:10::/28 comment="defconf: ORCHID" list=bad_ipv6
add address=3ffe::/16 comment="defconf: 6bone" list=bad_ipv6
/ipv6 firewall filter
add action=accept chain=input comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=input comment="defconf: drop invalid" connection-state=\
invalid
add action=accept chain=input comment="defconf: accept ICMPv6" protocol=icmpv6
add action=accept chain=input comment="defconf: accept UDP traceroute" port=\
33434-33534 protocol=udp
add action=accept chain=input comment=\
"defconf: accept DHCPv6-Client prefix delegation." dst-port=546 protocol=\
udp src-address=fe80::/10
add action=accept chain=input comment="defconf: accept IKE" dst-port=500,4500 \
protocol=udp
add action=accept chain=input comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=input comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=input comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=input comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=!LAN
add action=accept chain=forward comment=\
"defconf: accept established,related,untracked" connection-state=\
established,related,untracked
add action=drop chain=forward comment="defconf: drop invalid" connection-state=\
invalid
add action=drop chain=forward comment="defconf: drop packets with bad src ipv6" \
src-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: drop packets with bad dst ipv6" \
dst-address-list=bad_ipv6
add action=drop chain=forward comment="defconf: rfc4890 drop hop-limit=1" \
hop-limit=equal:1 protocol=icmpv6
add action=accept chain=forward comment="defconf: accept ICMPv6" protocol=\
icmpv6
add action=accept chain=forward comment="defconf: accept HIP" protocol=139
add action=accept chain=forward comment="defconf: accept IKE" dst-port=500,4500 \
protocol=udp
add action=accept chain=forward comment="defconf: accept ipsec AH" protocol=\
ipsec-ah
add action=accept chain=forward comment="defconf: accept ipsec ESP" protocol=\
ipsec-esp
add action=accept chain=forward comment=\
"defconf: accept all that matches ipsec policy" ipsec-policy=in,ipsec
add action=drop chain=forward comment=\
"defconf: drop everything else not coming from LAN" in-interface-list=!LAN
/system clock
set time-zone-name=MyTZ
/system identity
set name=HomeGW
/system note
set show-at-login=no
/tool mac-server
set allowed-interface-list=LAN
/tool mac-server mac-winbox
set allowed-interface-list=LAN
/tool sniffer
set filter-interface=ether1 filter-port=13231
The Wireguard server is the interface wireguard1 and the BTH is running in parallel as I am currently in location B.
I really don’t know what to try - I am out of ideas here…
Thank you in advance!