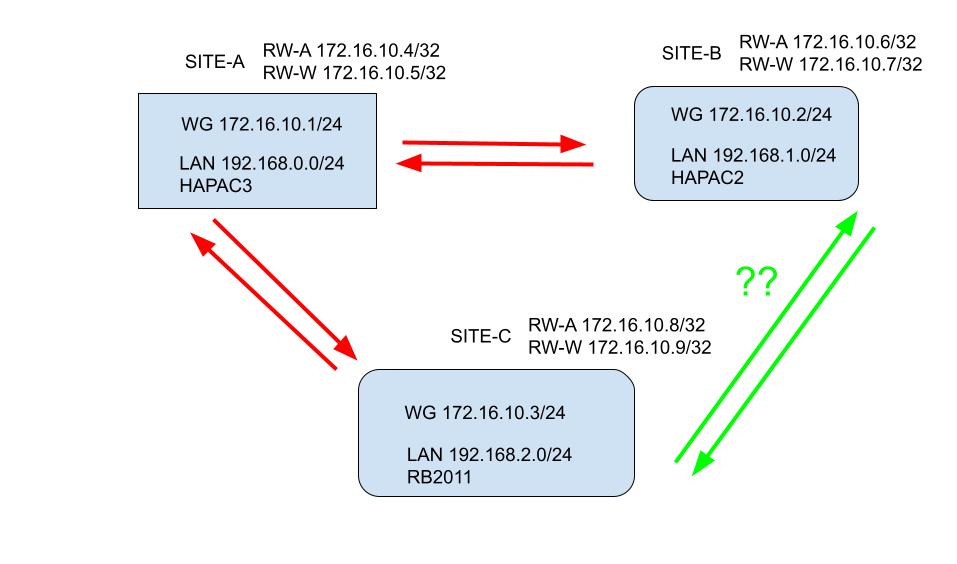
Okay so your concern is what if the server Router is removed from the picture.
The main reason why a tunnel would fail is if WAN connection was stopped or the router broke.
a. If the traffic failed on Server Router1 for handshake (either router1 failure or internet failure at R1) routers 2,3 would not be connected
b. If the traffic failed on a Client router 2 for handshake (either router2 failure or internet failure at R2 ) routers 1,3 would still be connected.
c. If the traffic failed on a Client router 3 for handshake (either router3 failure or internet failure at R3 ) routers 1,2 would still be connected.
Therefore the only possible redundant solution is another wireguard circuit between 2 and 3.
In the above scenario, lets play it out
a. Router1 is out of the picture, Router 3 connects to Router2 on secondary wireguard interface.
b. no effect 1 & 3 still talking
c. no effect 1 & 2 still talking
Therefore logically speaking we need one other wireguard interface/network and it can be up all the time ready to pitch in.
If you are willing to rely on a third party, you can run Zerotier network joining all three LANS such that they are on the same L2 subnet, whereas Wireguard connects them at L3.
The connection is from each router to Zerotier and thus any router failing has no effect on the other two connecting.
+++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++++
R1
Wireguard Interface=WG-MAIN1 listening port= 14555 comment=server on wireguard main.
allowed IPs=r2-wg-main2-IP/32,r2subnet comment=“client peer router2”
allowed IPs=r3-wg-main3-IP/32,r3subnet comment=“client peer router3”
/ip address
add address=10.10.10.1/24 interface=WG-MAIN1 network 10.10.10.0
/ip firewall
add action=accept chain=input dst-port=14555 protocol=udp comment='wireguard MAIN handshake"
add action=accept chain=forward src-address=localsubnet out-interface=WG-MAIN1 comment=“allow local subnet traffic to enter tunnel”
add action=accept chain=forward dst-address=localsubnet in-interface=WG-MAIN1 comment=“allow R2 and R3 subnet incoming traffic”
add action=accept chain=forward in-interface=WG-MAIN1 out-interface=WG-MAIN1 comment=“allow R2 to reach R3 and R3 to reach R2”
/ip route
add dst-address=r2subnet/24 gateway=WG-MAIN1 routing-table=main
add dst-address=r2subnet/24 gateway=WG-MAIN1 routing-table=main
R2
Wireguard Interface=WG-MAIN2 listing port=1455
Wireguard Interface=WG-ALT2 listening port=12555 Comment=server on wireguard alternate.
allowed IPs=wg-main1-subnet/24,r1subnet,r3subnet endpoint=publicIP-R1 endpointport=14555 persistent-keep-alive=35 comment=“server peer router1”
allowed IPs=wg-alt3-ip/32,r3subnet comment=“client peer router3”
/ip address
add address=10.10.10.2/24 interface=WG-MAIN2 network=10.10.10.0
add address=10.20.10.1/24 interface=WG-ALT2 network=10.20.10.0
/ip firewall
add action=accept chain=input dst-port=12555 protocol=udp comment='wireguard ALT handshake"
add action=accept chain=forward src-address=localsubnet out-interface=WG-MAIN2 comment=“allow local subnet traffic to enter tunnel”
add action=accept chain=forward dst-address=localsubnet in-interface=WG-MAIN2 comment=“allow R1 and R3 subnet incoming traffic”
add action=accept chain=forward src-address=localsubnet out-interface=WG-ALT2 comment=“allow local subnet traffic to enter tunnel”
add action=accept chain=forward dst-address=localsubnet in-interface=WG-ALT2 comment=“allow R3 subnet incoming traffic”
/ip route
add dst-address=r1subnet/24 gateway=WG-MAIN2 routing-table=main
add check-gateway=ping distance=1 dst-address=r3subnet/24 gateway=WG-MAIN1 routing-table=main
add distance=2 dst-address=r3subnet/24 gateway=WG-ALT2 routing-table=main comment=“use wireguard alternate if main is not available”
R3
Wireguard Interface=WG-MAIN3 listing port=1255
Wireguard Interface=WG-ALT3 listening port=1466
allowed IPs=wg-main1-subnet/24,r1subnet,r2subnet endpoint=publicIP-R1 endpointport=14555 persistent-keep-alive=35 comment=“server peer router1”
allowed IPs=wg-alt2-subnet/24,r2subnet endpoint=publicIP-R2 endpointport=142555 persistent-keep-alive=40 comment=“server peer router2”
/ip address
add address=10.10.10.3/24 interface=WG-MAIN3 network=10.10.10.0
add address=10.20.10.2/24 interface=WG-ALT3 network=10.20.10.0
/ip firewall
add action=accept chain=forward src-address=localsubnet out-interface=WG-MAIN3 comment=“allow local subnet traffic to enter tunnel”
add action=accept chain=forward dst-address=localsubnet in-interface=WG-MAIN3 comment=“allow R2 and R3 subnet incoming traffic”
add action=accept chain=forward src-address=localsubnet out-interface=WG-ALT3 comment=“allow local subnet traffic to enter tunnel”
add action=accept chain=forward dst-address=localsubnet in-interface=WG-ALT3 comment=“allow R2 subnet incoming traffic”
/ip route
add dst-address=r1subnet/24 gateway=WG-MAIN3 routing-table=main
add check-gateway=ping distance=1 dst-address=r2subnet/24 gateway=WG-MAIN3 routing-table=main
add distance=2 dst-address=r2subnet/24 gateway=WG-ALT3 routing-table=main comment=“use wireguard alternate if main is not available”