I started my Mikrotik journey in July of this year by introducing a RB4011 into a small business. My networking friends tried to discourage me from using the equipment by recommending other vendor that they felt were less complicated. You have to know your SH*&% to work with Mikrotik was their critism.
It has been a challenge but the equipment continues to exceed my expectations. My one takeaway is how versatile the router has been. I’ve implemented features I didn’t even know I needed when I started.
This forum has been a great resource since I started. I’ve come back to this waterhole to tap into those that have way more knowledge than me, to have a discussion on what I feel is my next step in network design.
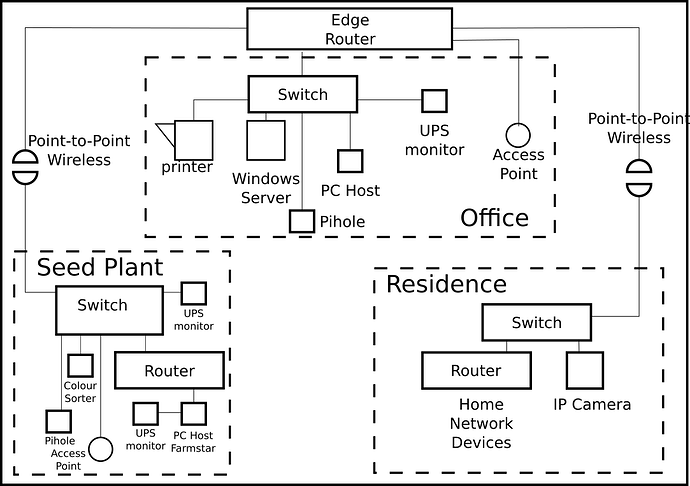
The current network design has the edgerouter (RB4011) providing three LAN subnets. Just LAN nothing else.
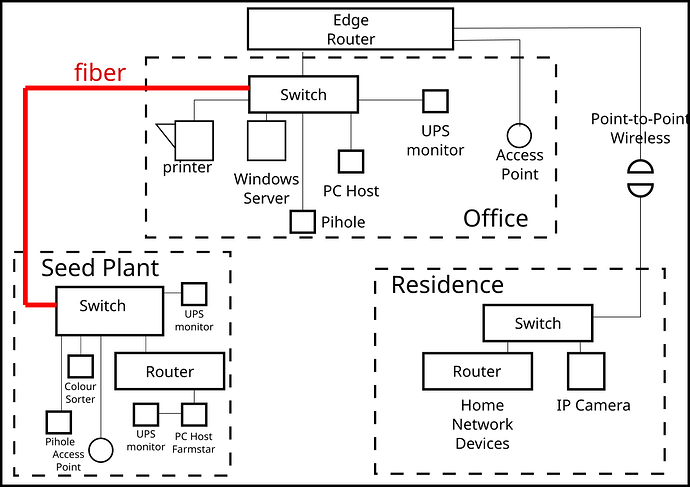
In January fiber will be installed that connects the switch in the Office to the switch in the Seed Plant. The switches are a Mikrotik CSS326 purchased in October. The point to point link that once supported the Seed Plant has been repurposed to support the Residence because the equipment is VLAN capable.
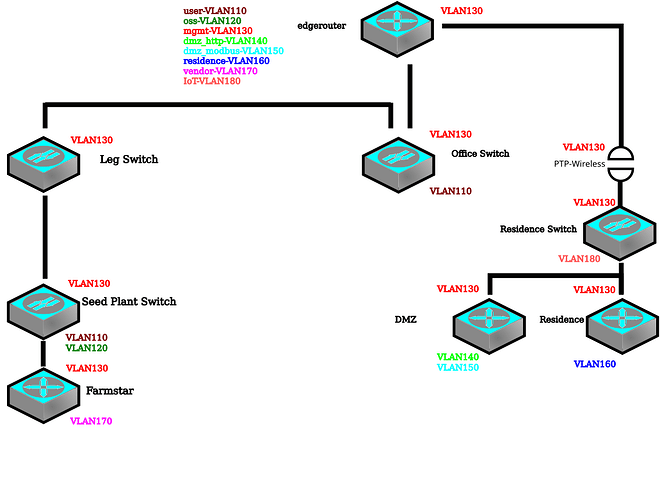
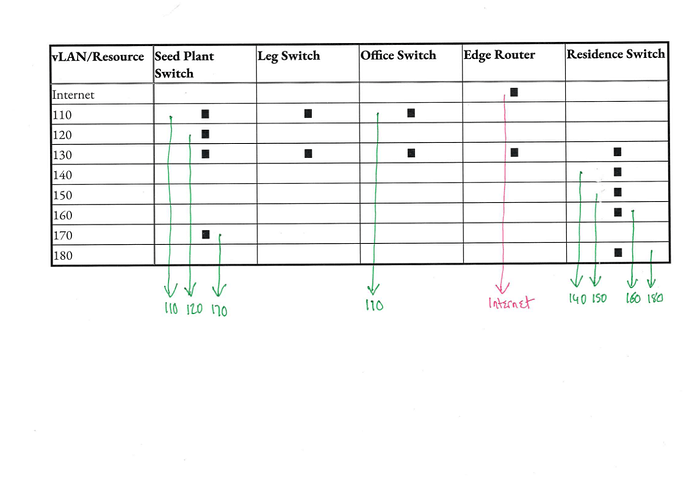
My plan is to reconfigure the edgerouter and implement three VLAN’s. The switches would be carved to provide LAN ports, OSS (Operational Support System) ports and MGMT (Management ports).
In the current network, LAN access is distributed to all sites. Many of the systems at the Seed Plant are not actually LAN devices but rather computers that run the operation. My goal is to VLAN the fiber backbone so I can better manage the traffic at the firewall.
The edgerouter would trunk the three VLANs to the switch in the Office. The trunk would extend to the switch at the Seed Plant. The Office and Seed Plant switches ports can be carved to support what is needed.
If successful I would move the point to point connection to the residence from the edgerouter to the Office switch and create a forth VLAN for network traffic from the residence. The current switch in the Residence is not VLAN capable so it would need to be replaced.
I’m looking for plus’s and minus’s. Critiques and criticism. What have I missed? Sharing your insight will help me know what I don’t know.
I’m new to network design. I retired in 2017 from a technology career. I started doing break-fix on this network and the role has expanded to CTO. I do all the work between break-fix and CTO.